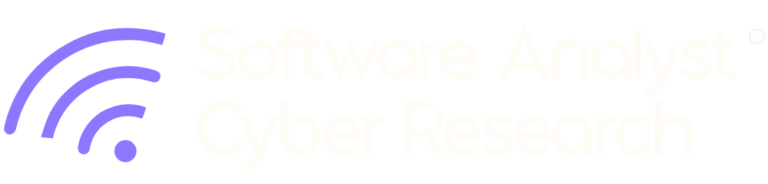
Executive Summary
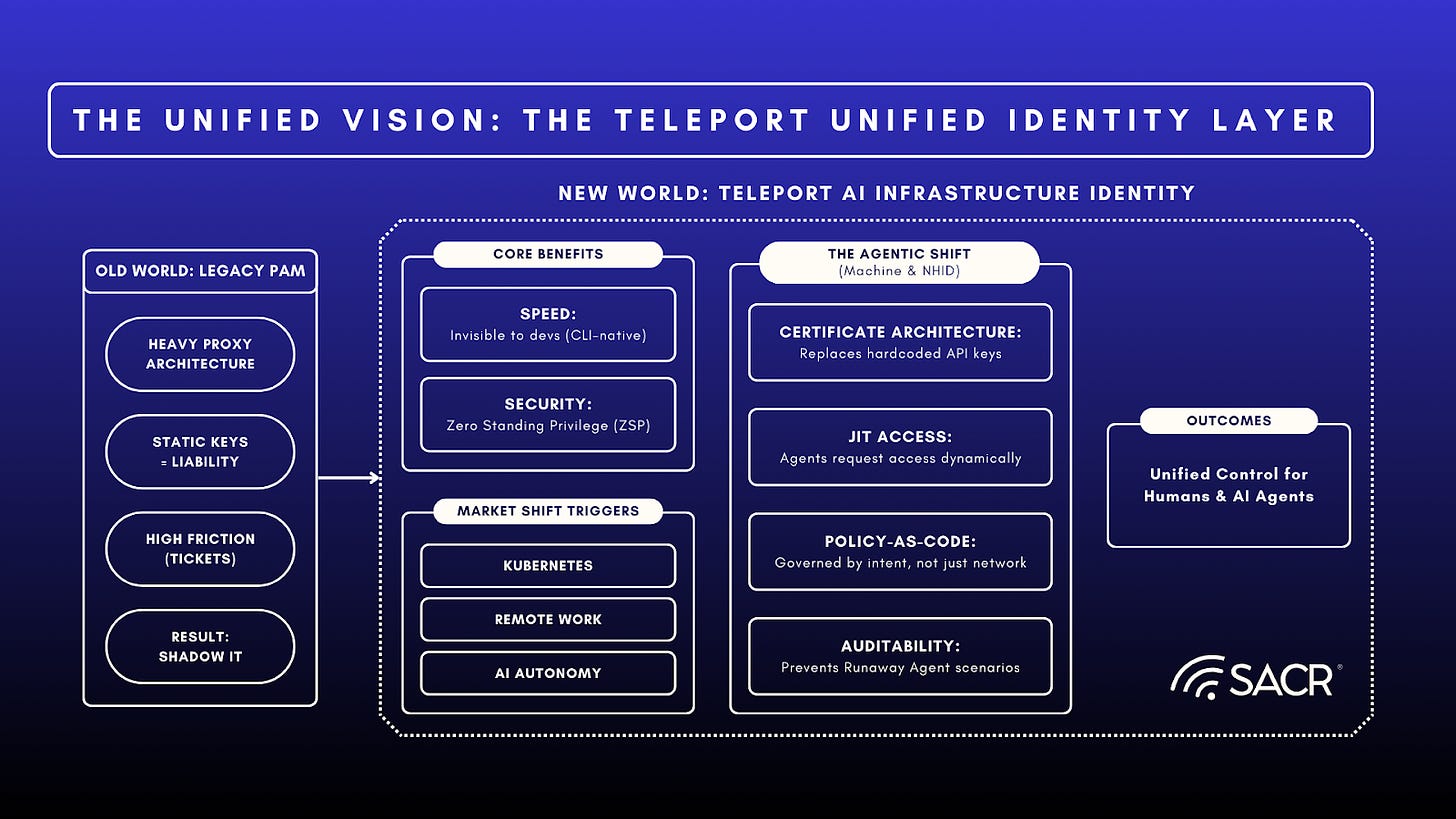
Security practitioners need to prioritize a fundamental reimagining of Privileged Access Management (PAM) and Identity Security, focusing on building from first principles around the concept of Infrastructure Identity. These changes are necessary because Legacy PAM vendors focus on vaulting long-lived credentials and rotating them, which adds friction and creates identity security risk exposure. The rapid adoption of AI agents is exacerbating the problem. Traditional identity tools cannot manage the non-deterministic nature of autonomous AI agents.
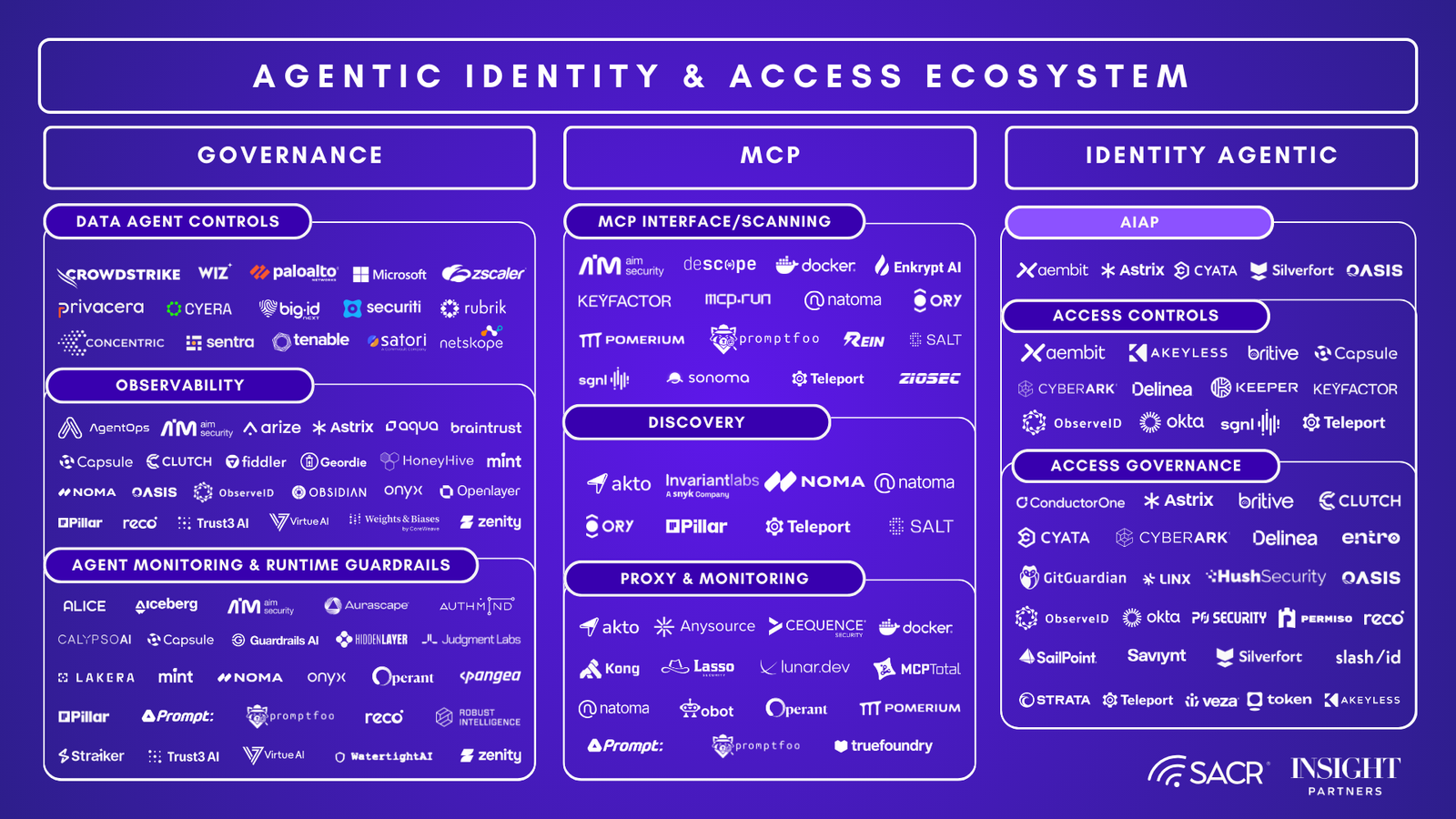
Vendors like Teleport offer a path to reimagining PAM. Rather than extending legacy vault-and-proxy architectures into cloud environments, they eliminate the need for secrets entirely through a hardware root of trust, the zero-standing-privilege (ZSP) model that is ideal for customers. They provide a Unified Identity Layer that is secured cryptographically. They act as real-time Certificate Authorities (CA), issuing short-lived, biometrically bound certificates that expire automatically. There are no secrets to steal or rotate. Moving to a unified identity control plane treats all identities, human, machine, workload, and AI agents, as first-class citizens. The approach eliminates the attack surface commonly associated with standing privileges while simultaneously accelerating developer productivity.
With over 600 customers, $50M-$100M in ARR, and deployments at leading financial services, technology and AI hyperscaler companies, Teleport has demonstrated enterprise-scale traction. Their platform’s core thesis is that privileged access should not exist when work is not being performed, a security invariant that eliminates the attack surface associated with standing privileges while simultaneously accelerating developer productivity.
Pioneering the Infrastructure Identity category
For decades, security has focused on managing secrets, vaulting passwords, rotating keys, and building higher walls around static credentials. Legacy PAM vendors were built for IT administrators in on-premise data centers, where their heavy, proxy-based architectures secured long-lived credentials. This Unified Access approach is increasingly deficient in this era of agentic AI and digital transformation. Static credentials in vault-based Unified Access environments comprise an attack surface.
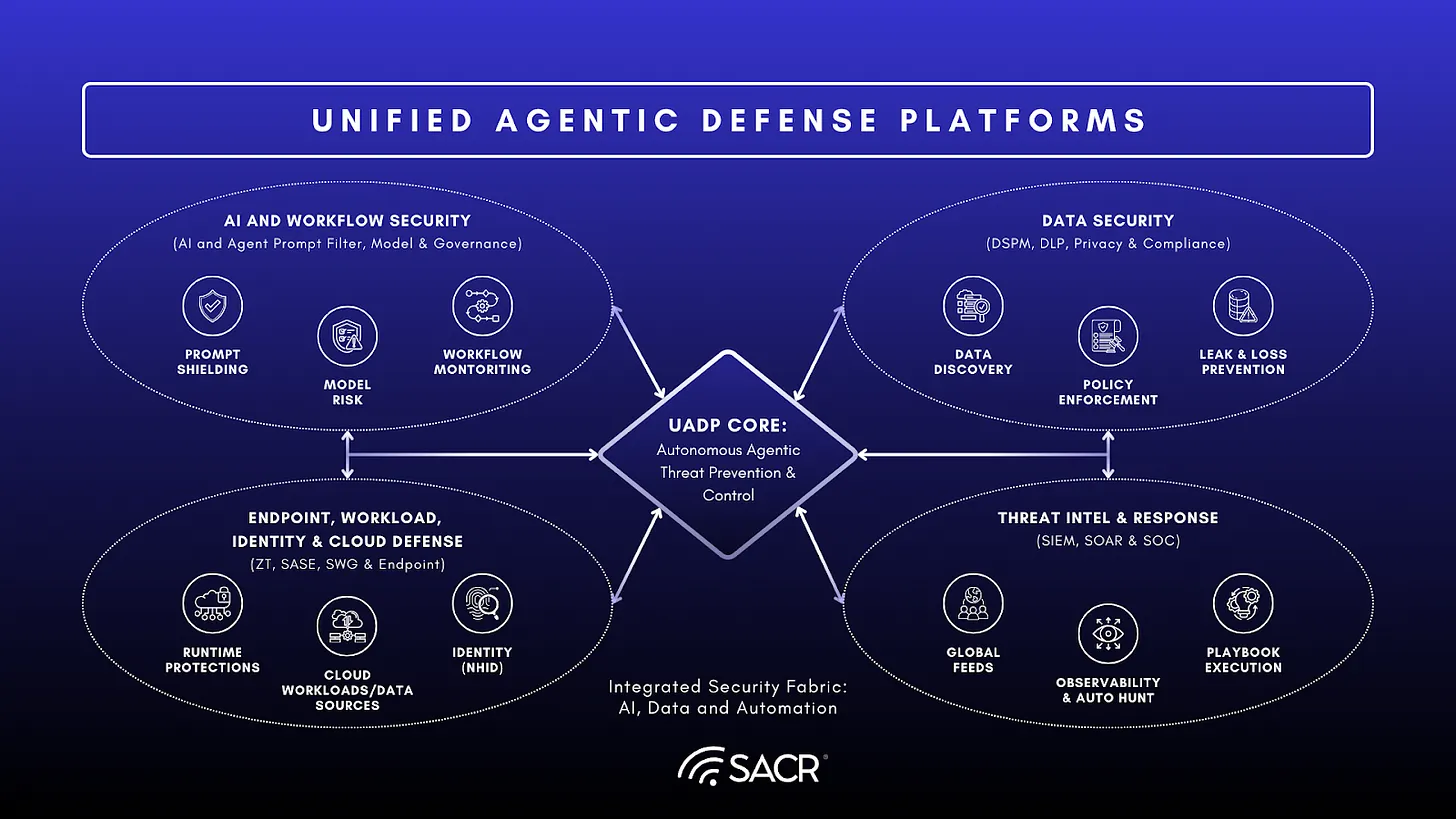
Teleport is part of a growing cohort that is pioneering the Infrastructure Identity category, which moves from Unified Access to Unified Identity by integrating the kind of robust access controls found in traditional PAM with the granular, dynamic entitlement and access management of Cloud Infrastructure Entitlement Management (CIEM) solutions. This approach addresses the core security challenge of unifying identity and providing secure, just-in-time (JIT) access across complex, multi-cloud, and hybrid environments.
Teleport eliminates the significant security liability posed by static, long-lived credentials like SSH keys and API tokens. It achieves this by replacing them with ephemeral, JIT access with a hardware root of trust, ensuring that access is strictly limited, short-lived, and adheres to the principle of least privilege. This innovative model is designed to secure both human engineers and the rapidly growing population of non-human AI agents and automated services.
Infrastructure Identity is based on establishing a single control plane for managing access controls and identity across AI agents, servers, applications, databases, Kubernetes, code repositories and Windows RDP environments.Teleport serves as an essential unified identity layer for modern infrastructure. This consolidated approach is critical for securing the next generation of agentic workflows, automated, AI-driven processes that require secure, audited, and ephemeral access to vital infrastructure resources.
Shifting to AI (agentic) Identity
In the latest Teleport release, the company is shifting to AI Infrastructure Identity, reflecting the increasing adoption of agentic identities within production infrastructure environments. This change extends the identity model, replacing traditional, vulnerable long-lived credentials (like passwords or static keys) with cryptographic identities and ephemeral authorization for AI agents The effect is to unify strong identity and access controls across humans, machines and workloads, and agentic identities using a modern, zero-trust approach to privileged access.
In this model, all AI agents, users, services, and machines must authenticate and authorize based on their identity before connecting to resources such as servers, databases, etc., with privileges governed by short-lived certificates that are scoped to the task and expire when the task is completed. This approach minimizes the attack surface, simplifies compliance, and ensures auditable, least-privileged access.
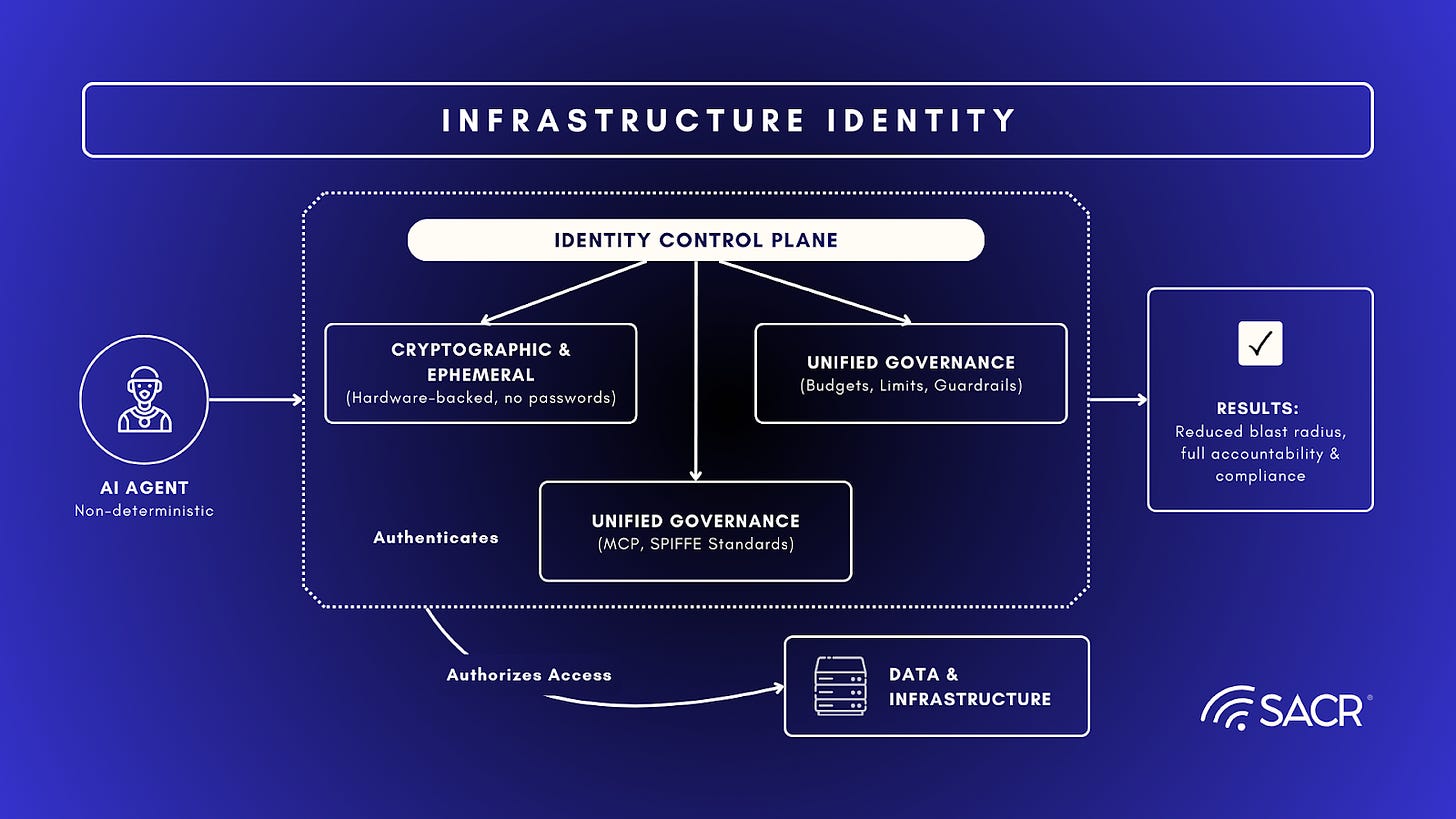
The Infrastructure Identity that Teleport has built offer several core technical pillars to ensure production-grade security:
- Cryptographic & Ephemeral Identity: Agents are treated as first-class citizens using hardware-backed, short-lived credentials rather than permanent, vulnerable passwords.
- Unified Governance: It centralizes control over AI budgets, rate limits, and access guardrails, providing real-time visibility into agent behavior.
- Standardization: By adopting open standards like MCP and SPIFFE, the framework prevents vendor lock-in and allows organizations to scale their AI deployments across diverse environments.
The Problem with Traditional Secrets Management
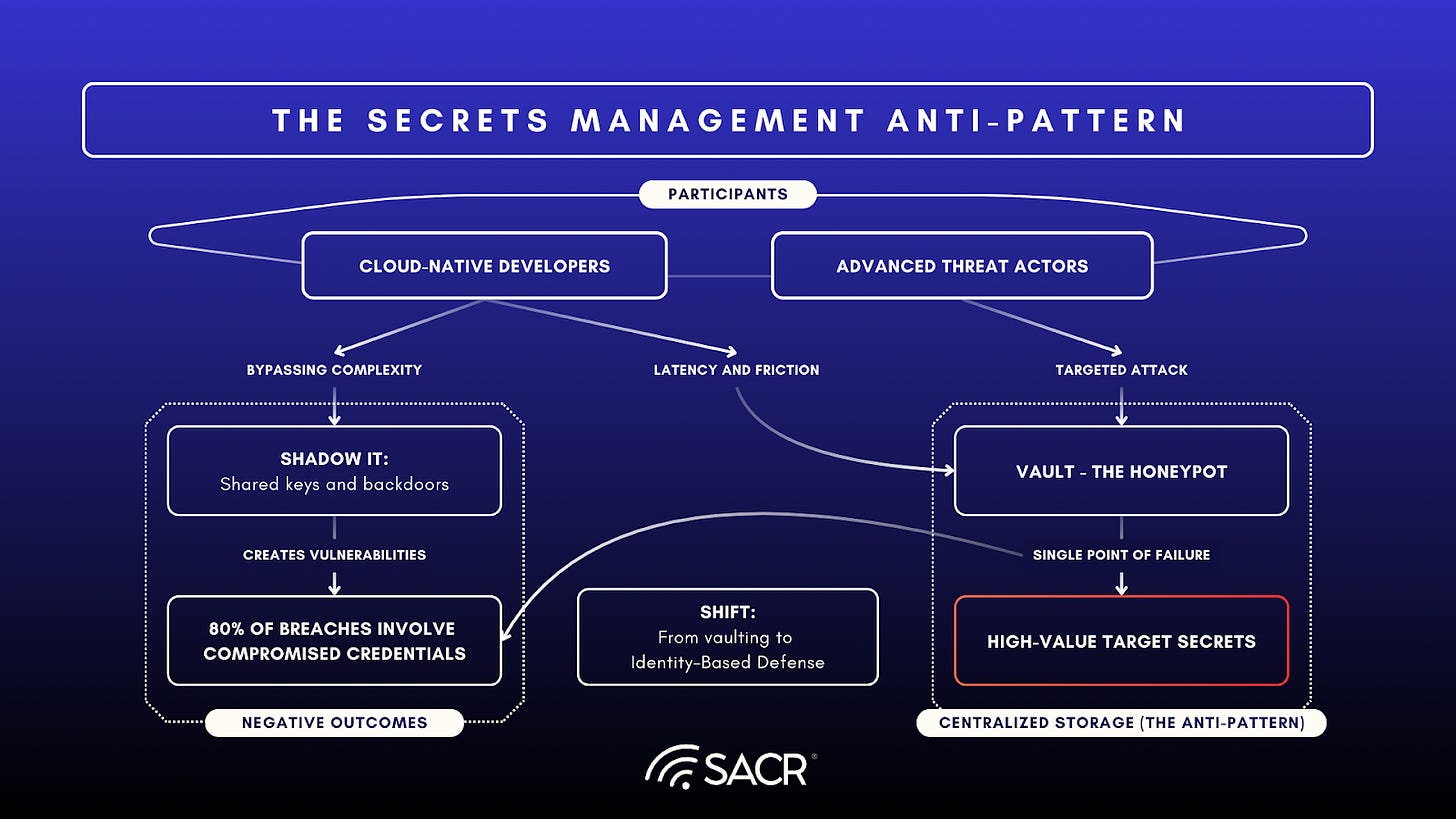
In a cloud-native, multi-cloud, and hybrid world, this vault-and-proxy approach is an anti-pattern.Secrets are commonly shared amongst various applications. Users regularly share secrets between themselves for ease and are generally subject to bad human behavior,even if there is no ill intention. It’s not so much a matter of needing better keys. It’s about needing to to stop using keys altogether.
Vaulting introduces latency and friction that cloud-native developers reject, leading to shadow IT and backdoor access methods and shared keys passing through various developer projects (because it’s tough to get new keys). Static credentials,even rotated ones, remain a persistent attack surface and a honey pot of secrets that tends to arise in vault based solutions. Such credentials become a critical target for advanced threat actors. This risk is all the more serious due to the rise of identity-based attacks. Indeed, 80% of breaches involve compromised credentials. Long-lived credentials are thus a massive liability, causing security practitioners and vendors to evolve and reconsider new concepts in identity and secret defense.
Market Context & Problem
1. The Pain Point
Modern engineering teams are grappling with a dual crisis driven by digital transformation, a process that combines exponentially increasing complexity and relentless pressure for higher velocity in software development and modifications to the IT estate. The complexity stems from managing high-growth, distributed, and fragmented identity infrastructure in environments that are operating at scale. They run across multi-cloud and hybrid environments. This result is an operational burden that includes having to meticulously manage, rotate, and audit a sprawling variety of secure access mechanisms, including SSH keys, Kubernetes configuration files, and highly sensitive database credentials. The need to identify and inventory identities is crucial in the new world of AI as AI cannot be deployed on top of environments with broad credential sprawl and overprivileged actors. This technical challenge is compounded by a severe security imperative, as 88% of security breaches now involve compromised credentials1, making the reliance on static secrets an unsustainable liability that dictates an urgent move toward a Zero Trust, identity-centric approach to access management.
2. The Legacy Failure
Legacy PAM solutions, optimized for monolithic, on-premise data centers and relying on heavy, proxy-based architectures, are fundamentally unsuited for the modern, cloud-native landscape. This reliance on centralized proxies and intermediary jump hosts introduces significant latency and friction into the developer workflow, a design that cloud-native developers, who prioritize speed and automation, overwhelmingly reject. The inherent architectural limitations of these legacy systems make it difficult, if not impossible, to natively support cloud-native protocols, ephemeral identities, or dynamic infrastructure, forcing organizations to bolt-on complex, often fragile, integrations that fail to deliver a seamless or secure experience. This friction-heavy model leads to a proliferation of shadow IT developers bypassing the restrictive PAM system by adopting less-secure methods like hard-coding credentials or using unmonitored backdoors which inadvertently creates significant security vulnerabilities and vast blind spots for security and compliance teams, ultimately defeating the very purpose of implementing a PAM solution.
3. The Market Shift
The shift to Cloud-Native Infrastructure, e.g.,Kubernetes, has accelerated the need for a solution that works everywhere without VPNs. Now, the AI/Agentic shift is driving the next wave, as machines need the same granular, governed access as humans. This approach resonates because it solves for both security through Zero Standing Privilege and speed, which is essential for developer experience (DX). Security becomes invisible to the developer, increasing velocity while tightening control. Engineers get a seamless, command-line-native (CLI-native) access experience without waiting for tickets or copy-pasting passwords.
Agentic Identity Framework
This shift allows enterprises to accelerate their AI adoption by replacing DIY security models with a standardized architecture. The approach reduces the blast radius of potential identity-based attacks and ensures that as AI agents become more autonomous, they remain fully auditable and compliant with corporate governance mandates.
Access Management: The Old Way vs. The Teleport Way
- The Old Way: Vault and proxy. Legacy PAM vendors focus on vaulting long-lived credentials and rotating them, adding friction and maintaining a honey pot of secrets.
- The Teleport Way: Unified Identity Layer secured cryptographically. Teleport acts as a real-time Certificate Authority (CA), issuing short-lived, biometrically bound certificates that expire automatically. There are no secrets to steal or rotate.
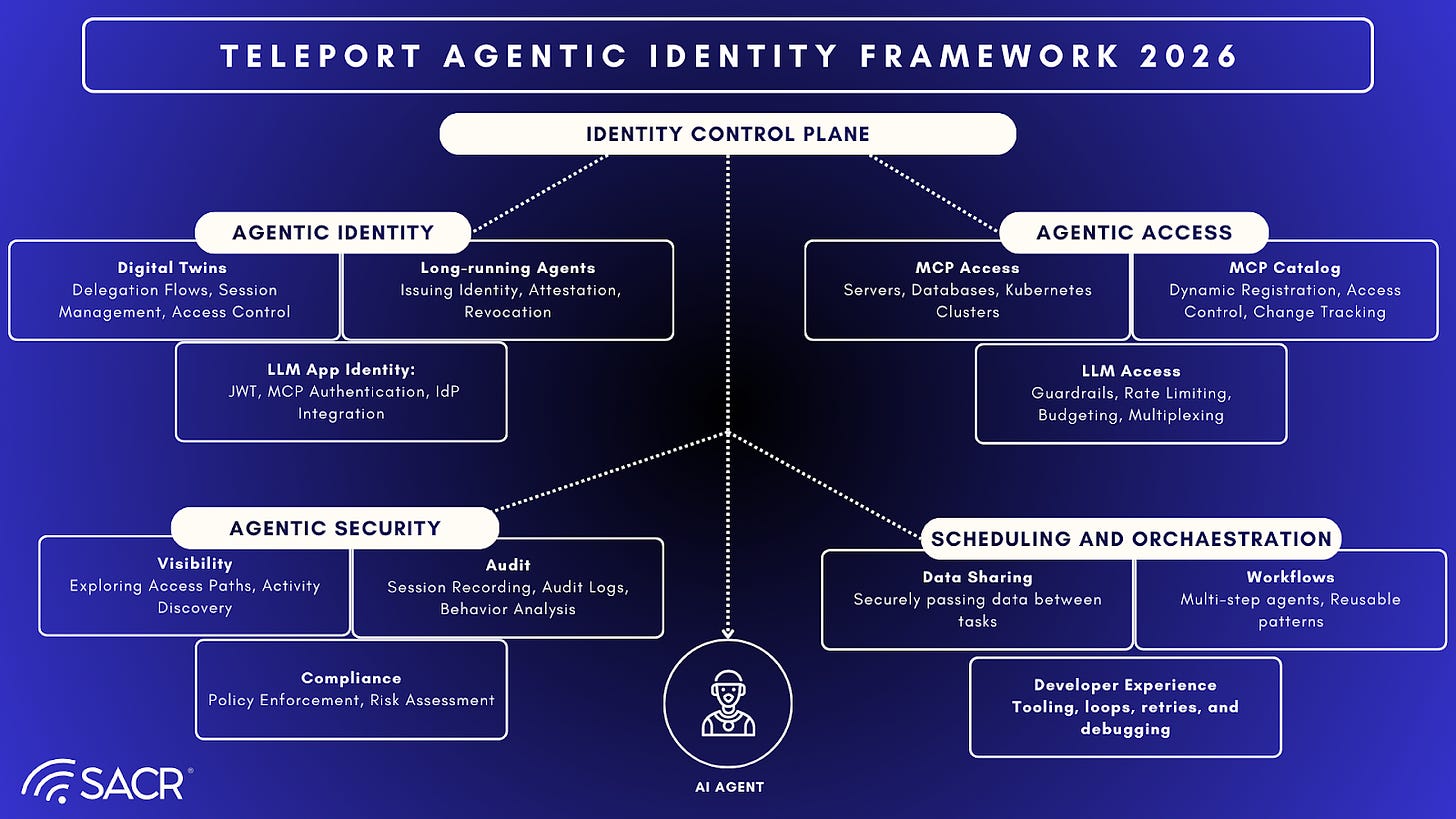
Due to the emergence of agentics, Teleport has shifted towards an Agentic Identity Framework which depicts key elements such as:
- Deploying agents safely across infrastructure
- Controlling and observing of LLM usage
- Operationalizing agent workflows in production
- Governing MCP-based access
- Detecting shadow agents and misbehavior
Zero Standing Privilege (ZSP) and Improved Developer Experience
This approach resonates because it solves for both security (Zero Standing Privilege) and speed (developer experience). Security becomes invisible to the developer, increasing velocity while tightening control. Engineers get Teleport Joy by moving to a more seamless, CLI-native access experience without waiting for tickets or copy-pasting passwords, while security teams get auditability and reduced blast radius. Teleport acts as a real-time Certificate Authority (CA), issuing short-lived, biometrically bound certificates that expire automatically. This eliminates the significant security liability posed by static, long-lived credentials (like SSH keys and API tokens), ensuring access is strictly JIT and adheres to the principle of least privilege.
AI and Infrastructure Identity
Teleport’s Agentic Identity Framework, launched in early 2026, which helps organizations address a critical security gap: traditional identity tools cannot manage the non-deterministic nature of autonomous AI agents. By moving away from static secrets and fragmented Identity and Access Management (IAM) systems, the Teleport Agentic Identity framework establishes identity as the primary control plane, ensuring that AI agents can interact with sensitive data and infrastructure without introducing unmanageable risk.
Teleport is basically a total revamp of how users get into the infrastructure. It works as a real-time cryptographically-sound Unified Identity Control plane, which is a fancy way of saying it hands out super-secure, short-lived certificates that are tied to users’biometrics and expire automatically. This is a game-changer because it directly fixes the huge security headache caused by old-school, never-changing credentials like hardcoded SSH keys, permanent database passwords, and API tokens that just hang around forever. By getting rid of these standing privileges, Teleport makes sure all access is strictly JIT and sticks to the least privilege rule, a must-have for modern Zero Trust security.
Benefits for All Stakeholders:
- For Security Teams: Security controls are significantly tightened. Teleport ensures Zero Standing Privilege, dramatically reduces the blast radius in case of a breach, and provides comprehensive auditability and logging for every connection. Security becomes stronger and control becomes clearer.
- For Developers and Engineers (The Teleport Joy): Teleport delivers an exceptional DX by making security an invisible enabler. Engineers gain a seamless, CLI-native access experience. This eliminates annoying workflow delays. There is no more waiting for tickets or human approval, or tedious copying and pasting of passwords. This increased velocity is critical.
- For Teleport and its customers: It is a win-win solution that achieves the critical objective of boosting developer speed while simultaneously strengthening security oversight and controls. By replacing static passwords and secrets with a dynamic, cryptographically sound Unified Identity Control plane, the entire access workflow is streamlined and secured.
The New Challenge: The market shift is now being driven by the AI/Agentic shift. It’s no longer just humans who need access to digital assets. As AI agents and autonomous workloads are exploding, requiring secure, audited, and ephemeral access to vital infrastructure resources. Giving an AI agent a hardcoded API key or static secret is a recipe for disaster, e.g., due to runaway agents or lateral movement. Teleport’s Infrastructure Identity model is designed to secure the rapidly growing population of non-human AI agents and automated services.
They must be treated as first-class citizens with their own identity through:
- Teleport Machine ID: Identity for workloads, e.g.,CI/CD or bots, using the same certificate-based architecture to replace hardcoded API keys.
- Just-in-Time Access: Agents should request access dynamically.
- Policy Governance: They must be bound by policy-as-code, i.e.,what they can do, not just network reachability.
- Auditability: Every action must be auditable back to the specific agent identity, preventing runaway agent scenarios.
The Unified Vision: The Teleport Unified Identity Layer
The Unified Identity Layer centers on consolidating access, governance, and security across all types of identities into a single, cohesive platform.
The core of this vision is the recognition that modern infrastructure relies not just on human engineers, but increasingly on machines, workloads, and AI agents. Managing these separate identity silos creates security vulnerabilities and slows down engineering velocity.
Teleport’s Unified Identity Layer vision is built on several key principles and components:
1. Universal Identity Consolidation
Teleport aims to unify all identities under one strong, cryptographic identity framework. This eliminates the need for fragmented, legacy access methods like static SSH keys, VPNs, or shared database credentials. The layer secures:
- Human Identities: Engineers and third-party contractors.
- Machine & Workload Identities: Servers, microservices, and automated CI/CD pipelines.
- AI & Agentic Identities: LLMs, autonomous agents, and systems using the Model Context Protocol (MCP).
2. The Four Pillars of the Platform
To realize this unified vision, the Teleport Infrastructure Identity Platform integrates four distinct control mechanisms:
- Zero Trust Access: Eliminating standing credentials and replacing them with short-lived, ephemeral certificates. This ensures least-privileged access without relying on network perimeters. There is no more need for VPNs or bastion hosts.
- Machine & Workload Identity: Securing and governing inter-machine interactions so that automated systems authenticate with the same rigor as human users.
- Identity Governance: Implementing JIT access requests, enabling robust auditing, and automating on/off-boarding. This hardens identities and accelerates compliance, e.g., forFedRAMP, SOC 2, HIPAA, etc.
- Identity Security: Exposing and eliminating hidden risks, such as risky shadow access paths or vulnerabilities resulting from an Identity Provider (IdP) compromise.
3. Securing Both Classic and AI Infrastructure
A major part of Teleport’s modern vision is ensuring that the rise of Agentic AI doesn’t break enterprise security. The Unified Identity Layer treats AI agents as first-class citizens. By applying the same Zero Trust and Identity Security principles to AI, organizations can safely implement MCP tools and allow LLMs to interact with databases and internal APIs without exposing the infrastructure to context-poisoning or shadow agent attacks.
The Ultimate Goal: Velocity + Resiliency
Teleport’s unified vision argues that security and speed are not mutually exclusive. By unifying human, machine, and AI identities into one layer, organizations can achieve:
- For Engineers: Reduced toil, instant access to necessary resources, and automated workflows.
- For Security Teams: A reduced attack surface, zero standing privileges, and highly centralized, audit-grade visibility across the entire hybrid cloud.
- Unified Protocol Support: Handling SSH, K8s, DBs, and Windows in one tool is technically hard to replicate, giving Teleport a key technical moat.
- Protocol-Aware Proxying: The technical differentiator is the protocol-aware proxying combined with certificate-based auth, allowing deep inspection and session recording.
Company History & Founding Story
Origin Story
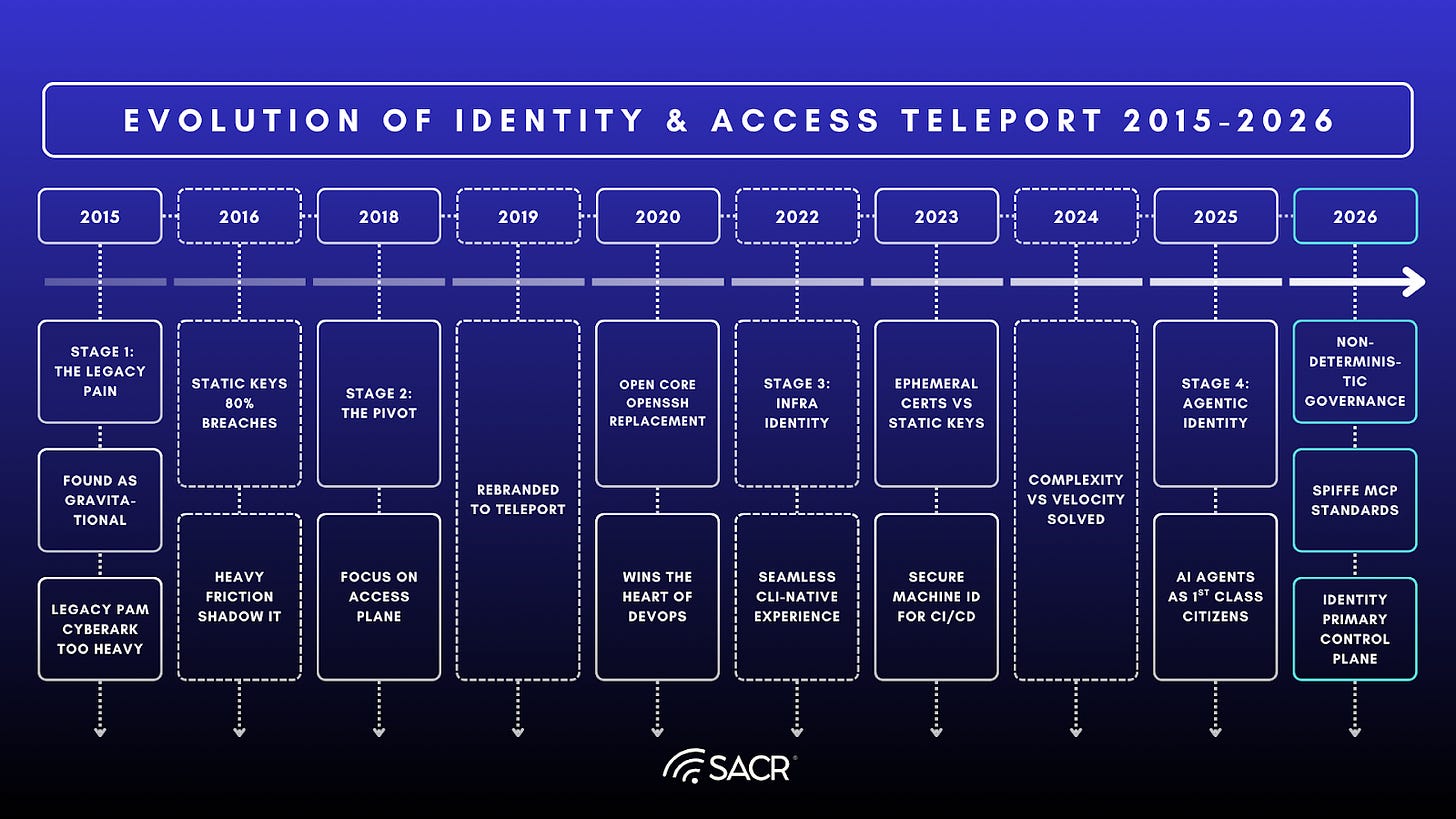
Founded in 2015 as Gravitational, the company was started by Ev Kontsevoy (CEO), Alexander Klizhentas (CTO), and Taylor Wakefield (COO). They previously started Mailgun together, which was acquired by Rackspace. While at Rackspace, Kontsevoy was responsible for developing “OnMetal” bare metal OpenCompute servers which developers could provision in seconds via API or UI. Gravitational was started based on their experiences at Rackspace, where they saw the difficulties related to deploying and managing applications across cloud and on-premise infrastructure.
Course Correction
The company started with a broader focus on application portability.ts original product, Gravity, was a tool to package apps for on-prem delivery and management. Teleport was originally an open source library developed by Klizhentas to access these application environments and was not intended to be a separate commercial product. They realized the access plane component was the killer app and rebranded effectively to Teleport in 2020 to focus entirely on the infrastructure access problem.
Early Traction
Teleport gained traction through an Open Core model. By open-sourcing the base protocol, they won the hearts of DevOps engineers who could just use it to replace OpenSSH. This bottom-up adoption created a groundswell that translated into enterprise deals as those companies grew.
Teleport Product Ecosystem Deep Dive
The Platform View: Unified Identity Layer
Teleport also operates as a Unified Identity Layer with its Identity control plane as a consistent identity perimeter. It sits between identities (Okta, AD, Github) and infrastructure (Servers, K8s, Databases, Apps, Windows Desktops). It consolidates connectivity, authentication, authorization, and audit into a single platform.
Component Breakdown
- Teleport Access (Core): The flagship connectivity layer replacing SSH/VPNs with identity-aware proxies.
- Teleport Identity Governance: Unified access requests, approvals, and recertification workflows built-in, replacing separate IGA tools.
- Teleport Machine ID: Identity for workloads, e.g.,CI/CD and bots, using the same certificate-based architecture, replacing hardcoded API keys.
- Teleport Identity Security: Which traces the full chain of identity across Okta, Teleport, AWS, GitHub, and more, turning fragmented logs into actionable insight and enforceable control.
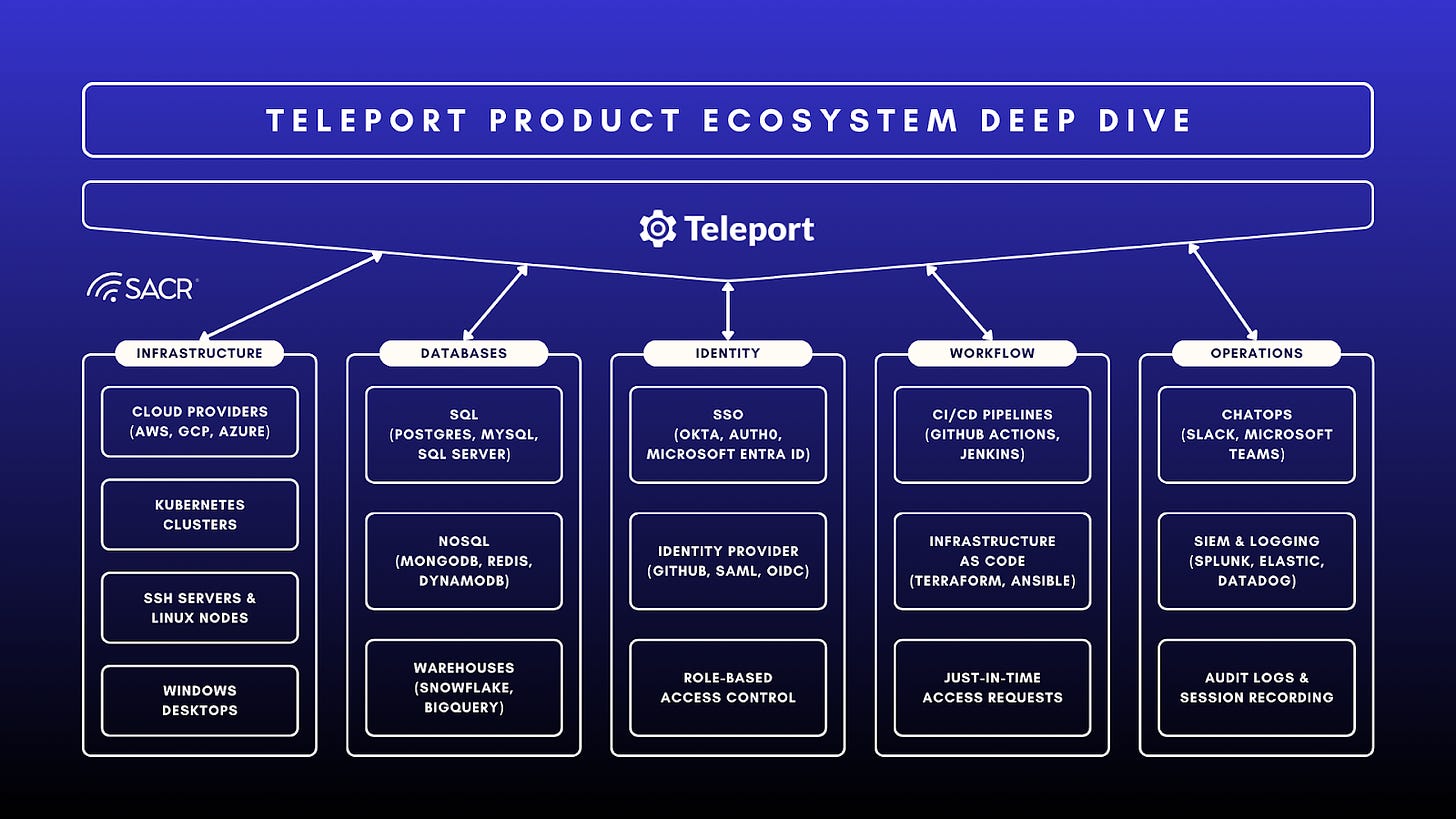
Teleport Product and Go-To-Market Summary
Teleport’s key technical differentiator is the protocol-aware proxying it provides combined with certificate-based auth. Teleport understands the protocols, e.g.,SSH, RDP, Postgres wire protocol, etc., allowing it to provide deep inspection and session recording without needing agents on every target in some configurations, while the certificate architecture ensures zero trust.
Teleport offers a Developer-First User Experience that is CLI-centric (tsh login, tsh ssh) and integrates with standard tools like VS Code and terminal clients, allowing engineers to maintain their existing workflows.
Their Go-To-Market (GTM) strategy uses a sales led with engagement with:
- VP of Infrastructure Operations
- VP of Infrastructure Security
- Platform Engineering Lead / Platform Engineering org
- Security leadership such as CISO / VP of Security
- Security teams
- SOC / SecOps
- DevOps / SREs
Teleport also leverages Cloud Marketplaces such as AWS and GCP for procurement and offers deep integration with Identity Providers like Okta and Auth0. The company is developing a partner ecosystem focused on Identity Security integrators.
Teleport Target Personas
- Primary: VP of Engineering / Platform Engineering Lead (wants velocity).
- Secondary: CISO / VP of Security (wants compliance and audit).
- User: DevOps/SREs (wants ease of use).
Financial & Growth Analysis
Teleport grew from a small open-source project to $50M-100M ARR, with a recent acceleration driven by the Identity Security consolidation trend. Growth rates have been cited as robust (4.5x net new ARR at Series C peak), though stabilizing at enterprise scale. Total funding for Teleport is approximately $169 million across four funding rounds. The company raised $110M in a Series C round in May 2022 at a $1.1 Billion valuation. Teleport is backed by Bessemer Venture Partners, Insight Partners, Kleiner Perkins, and S28 Capital. This unicorn status validates their market approach.
Community & Market Validation
Beyond revenue and funding, Teleport has secured deep developer loyalty with ~20k GitHub stars and ~2k forks2, validating their open-core strategy. Their market impact was recently cemented by their inclusion in the 2026 Fortune Cyber 603 and winning the 2025 AI in Cybersecurity Innovation Award4 and the 2025 AWS Rising Star Partner of the Year award. Operationally, they remain efficient with approximately 250 employees while serving a massive enterprise scale, including three of the top five global financial institutions and AI hyperscalers. 86% of organizations cannot guarantee that former engineers do not continue to have access to production environments5. This zombie access risk is a primary driver for Teleport’s ephemeral certificate model.
Competitive Landscape
Teleport most often competes against incumbent PAM in hybrid enterprises, and internal DIY / cloud-native builds in platform-forward orgs. Direct modern infra access competitors exist, but many deals are decided by whether the buyer wants an identity-centric control plane across protocols versus point solutions.
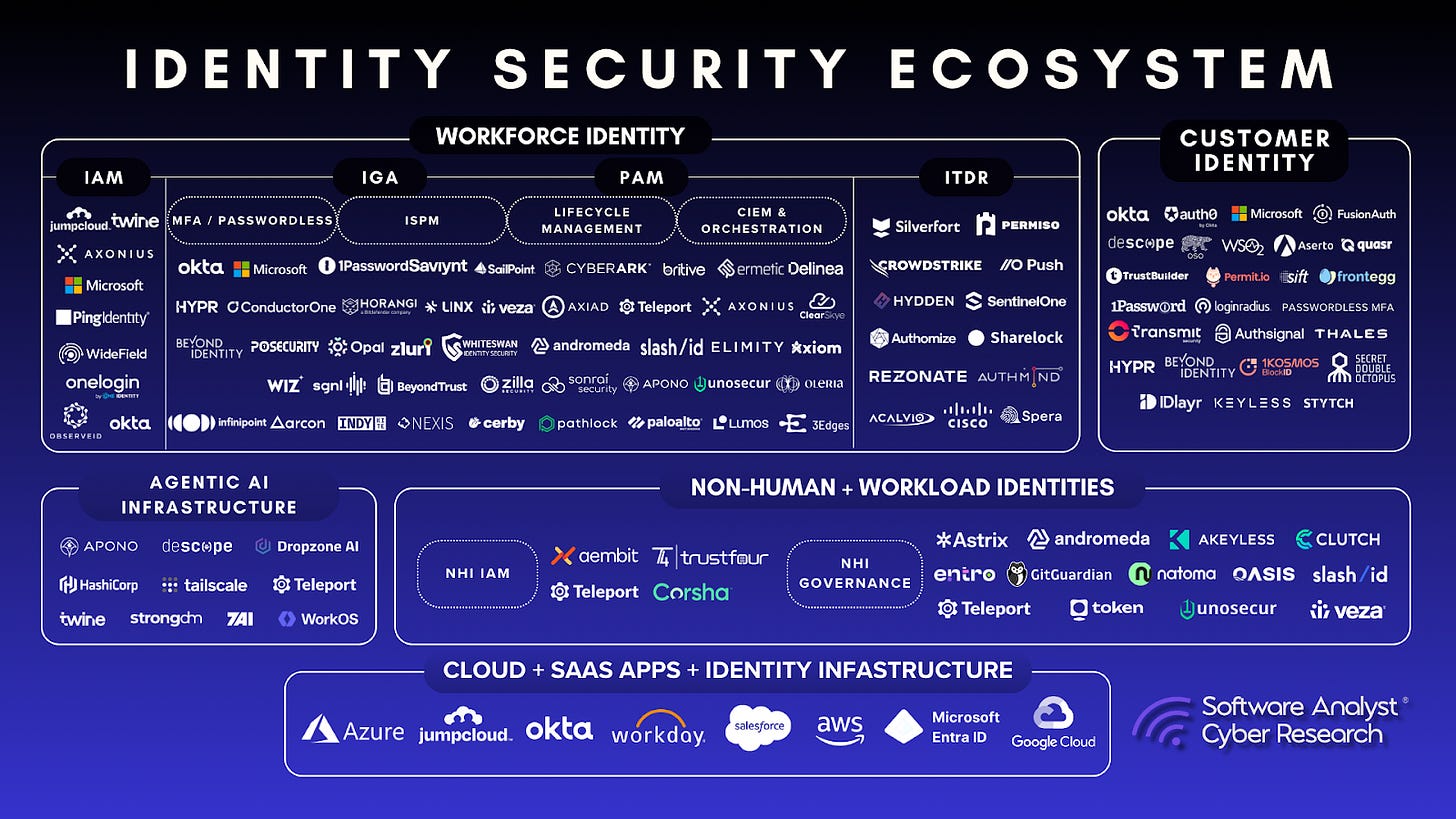
Incumbents, DIY / hyperscaler-native
- DIY / Cloud-native builds (AWS IAM + SSM/EC2 Instance Connect, Azure, GCP, plus OSS): Common default path for platform teams.
- DIY is one of the most frequent competitive situations. This approach often leads customers to engage later. Teleport wins when customers want to reduce bespoke operational/security engineering and get unified audit, governance, and multi-protocol support.
- CyberArk: Tends to be a category leader in legacy PAM entrenched in hybrid/on-prem where typically evaluated for IT admin and Windows-heavy environments.
- BeyondTrust/Delinea: They are established PAM vendors, modernizing for cloud workflows, strength in traditional privileged credential workflows.
The Modern Rivals
- StrongDM: StrongDM focuses more on ease of use across broad protocols, while Teleport goes deeper on security/compliance and open source.
- HashiCorp Boundary: An open-source alternative for secure access, but less mature in enterprise governance features.
- Microsoft Entra: As Microsoft expands Entra Private Access, they become a platform threat.
The Teleport Moat
- Unified Protocol Support: The ability to handle a wide array of infrastructure protocols including SSH, Kubernetes (K8s), Databases (DBs), Model Context Protocol (MCP), Windows (RDP) and Git all within a single tool.
- Protocol-Aware Proxying: This technical differentiator, combined with their certificate-based authentication, allows for deep inspection and session recording while ensuring Zero Trust.
- Open Source Community: A massive barrier to entry.
- Teleport Joy: The strong developer love and brand loyalty and a unified platform that brings together zero trust access, identity governance and identity security.
Future Outlook
Future Competitive Landscape (2026–2029)
The next phase of competition around Infrastructure Identity will be defined less by PAM vs. modern access and more by who becomes the default control plane for non-human identity across hybrid infrastructure, SaaS admin surfaces, and AI-agent tooling. Teleport’s competitive set will likely expand in three directions at once: cloud providers moving up-stack, identity incumbents moving down-stack, and security platforms converging toward governance and detection for agentic workflows.
1) Cloud and hyperscaler-native access becomes good enough:
AWS, Microsoft, and Google will continue to produce secure access primitives that reduce the perceived need for a standalone access layer. Expect steady improvement in:
- Managed, identity-integrated access paths to compute and private apps.
- Session logging, conditional access, and policy controls.
- Procurement simplicity where buyers already pay these vendors, and features arrive as bundle enhancements.
Implication: Teleport will increasingly need to win on cross-cloud, cross-protocol unification, and on capabilities that are difficult for hyperscalers to deliver outside their own ecosystem. This will be especially relevant for heterogeneous environments and regulated audit requirements.
2) Identity giants converge into infrastructure access and governance:
Okta and Microsoft,and, to a lesser degree, other identity ecosystems, will keep extending identity policy solutions deeper into the infrastructure layer. The likely path will include:
- Identity-first private access expands from web apps to developer and operator workflows.
- Security teams demand tighter linkage between user identity posture, device posture, and privileged activity.
- Governance features become table stakes, e.g., access requests, approvals, recertification, and audit workflows.
Implication: The market will increasingly evaluate Teleport not just for access, but as an identity governance and enforcement layer for infrastructure and non-human identities, where differentiation depends on depth of protocol-level control and auditability.
3) PAM incumbents modernize through acquisitions and platform rewrites:
Incumbent PAM vendors will keep investing in cloud-friendly architectures and buying CIEM, identity analytics, and posture capabilities. Over time, the category language may shift toward identity security platforms rather than PAM.
Implication: Competitive displacement will become harder to summarize as legacy vs modern. Teleport will face more hybrid modernized stacks where a buyer wants to rationalize tools without losing legacy coverage,especially in Windows-heavy and mainframe-adjacent use cases. Co-existence will remain common in large enterprises.
4) CNAPP and security data platforms will push into “agent governance”:
As agentic workflows move from experimentation to production, CNAPP vendors and security analytics platforms will try to own the agent control story via:
- Runtime detection of abnormal tool use and privilege escalation.
- Correlating agent behavior with identity signals, workload context, and cloud activity logs.
- Policy recommendations based on observed behavior, e.g.,you only used these actions, so restrict scope.
Implication: Many platforms will offer strong visibility, but struggle to deliver enforcement across heterogeneous protocols and identity types. The competitive battleground becomes who can both observe and constrain agent actions with auditable, least-privilege identity controls.
5) A fragmented Model Context Protocol (MCP) security ecosystem is emerging:
A wave of point solutions will appear around MCP catalogs, tool allowlists, prompt/tool policy, and agent firewall concepts. Some will be thin wrappers around model providers, while others will be enterprise-grade governance layers.
Implication: This space will be noisy and crowded. Buyers will eventually consolidate toward solutions that can connect agent governance back to concrete infrastructure identity controls, approvals, and chain-of-custody auditing.
6) The core buying center will shift toward platform security and engineering leadership:
As security responsibility continues moving closer to platform engineering, competitive evaluations will prioritize:
- Developer workflow compatibility and speed.
- Low operational overhead at scale.
- Audit and governance that does not require constant manual process.
Implication: Winning will require combining a strong platform story with measurable security outcomes, not just better access.
The Next Frontier
In January 2026, Teleport formally launched the Teleport Agentic Identity Framework, pivoting it aggressively to secure the rapidly expanding non-human workforce. Moving beyond simple access, Teleport now positions identity as the missing control plane for AI, arguing that observability tools can see what agents do, but only identity can control what they are allowed to do. Teleport’s strategy shifts the security focus from protecting the network perimeter to controlling and verifying the identity and intent of the entity attempting access, creating a fundamentally secure, identity-centric infrastructure mesh that is ready for the agentic era.
With native support for the MCP and SPIFFE standards, Teleport aims to be the governance layer that prevents runaway agent scenarios. By introducing a Governed MCP Layer, Teleport allows organizations to enforce access control and identity security, treating them as first-class, cryptographically secured identities rather than relying on brittle static secrets. This positions Teleport uniquely at the intersection of three massive trends: Platform Engineering, Identity Security Consolidation, and the Agentic AI Revolution. They have successfully crossed the chasm from a developer tool to a critical enterprise security platform, arguing that their Infrastructure Identity thesis,replacing static credentials with ephemeral, cryptographic trust, is the prerequisite for deploying AI in production.
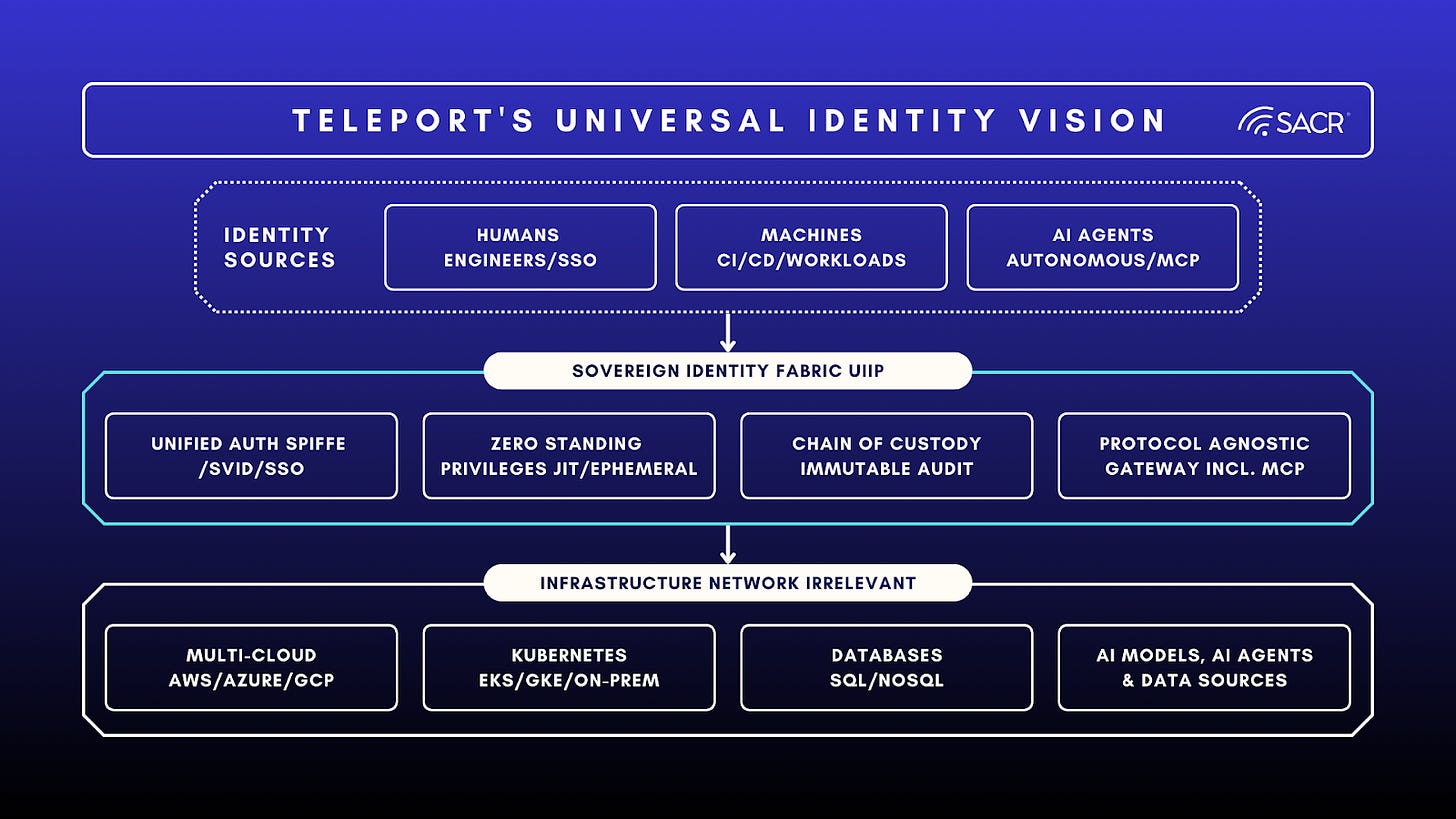
Teleport’s Universal Infrastructure Identity Vision
Teleport aims to become the Universal Infrastructure Identity Provider (UIIP), establishing a Sovereign Identity Fabric where every interaction whether it be human, machine, or autonomous agent is brokered, authenticated, and audited by Teleport, making the underlying network irrelevant. This ambitious goal transcends traditional perimeter security models by serving as the mandatory intermediary for all infrastructure access, abstracting away the complexity and inherent insecurity of fragmented cloud networks.
In this model, the physical or virtual location of a resource, whether on-premises, in a multi-cloud environment likeAWS, Azure, or GCP, or within a Kubernetes cluster, becomes irrelevant. The focus shifts entirely to the identity-native control plane.
The core pillars of the Teleport vision are:
- Unified Identities (Human & Machine): Providing a single control plane that unifies engineers via SSO/IdPs and workloads via Teleport Machine ID and SPIFFE-compatible SVIDs. This ensures that CI/CD pipelines, microservices, and AI agents operate under the same rigorous trust standards as human users, eliminating the “Secret Zero” problem.
- Zero Standing Privileges (ZSP): Implementing JIT access policies that grant ephemeral, cryptographic certificates only for the duration of a task. This eliminates the attack surface of long-lived static credentials, ensuring that no user or agent holds permanent access to critical infrastructure.
- Identity-Aware Auditing & Chain of Custody: Creating an immutable, time-stamped, and searchable audit log that captures not just who accessed a resource, but the full chain of custody. This is critical for agentic AI, where security teams must trace an action back from an autonomous agent to the human who authorized its goal.
- Protocol Agnosticism,including for MCP: Supporting a wide array of infrastructure protocols, SSH, Kubernetes API, databases like PostgreSQL andMongoDB, Windows RDP, Git, and internal web applications,while now acting as a secure gateway for the MCP. This allows Teleport to govern how AI models interface with sensitive data sources, enforcing schema-level access controls.
Teleport’s Universal Infrastructure Identity Vision
Teleport Adoption Risks
- Agent-Heavy Architecture: Teleport generally requires agents (or tbot binaries) on end resources,or at least within the network. This contrasts with some agentless competitors, potentially increasing administrative overhead for managing the Teleport agents themselves in self-hosted configurations.
- Ecosystem Isolation: Some competitors argue that Teleport does not easily integrate with other elements of the broader security ecosystem like existing IGA tools or vaults. This perceived lack of easy integration, potentially forces organizations to replicate investments in device posture or identity governance rather than leveraging existing stacks.
- Commoditization by Cloud Providers: AWS or Azure building Teleport-like zero-trust access directly into their platforms,e.g., AWS Instance Connect.
- Platform Convergence: Identity giants likeOkta or Microsoft moving down the stack into infrastructure access.
SACR Take Away
Final Verdict
SACR is Bullish on Teleport as they continue to evolve their solution and take on new challenges. Teleport is uniquely positioned at the intersection of three massive trends: Platform Engineering, Identity Security Consolidation, and AI Agentic Access. They have successfully crossed the chasm from a developer tool to an enterprise security platform. Their Infrastructure Identity thesis is the correct architectural answer for the cloud/AI era. The company will need to advance its intent awareness capability, but we advise to stop buying better vaults. Start architecting for identity. As organizations adopt agentic workflows, the ability to govern non-human identity will be the difference between innovation and breach.
Citations:
1 Verizon Data Breach Report 2025
2 Teleport Community Edition (GitHub)
3 Teleport named to Fortune Cyber 60