Runtime Security for AI Agents: An Identity Governance Perspective
About Authors Kevin He is a Principal at MVP Ventures, where he focuses on infrastructure software and cybersecurity investments from
About Authors Kevin He is a Principal at MVP Ventures, where he focuses on infrastructure software and cybersecurity investments from
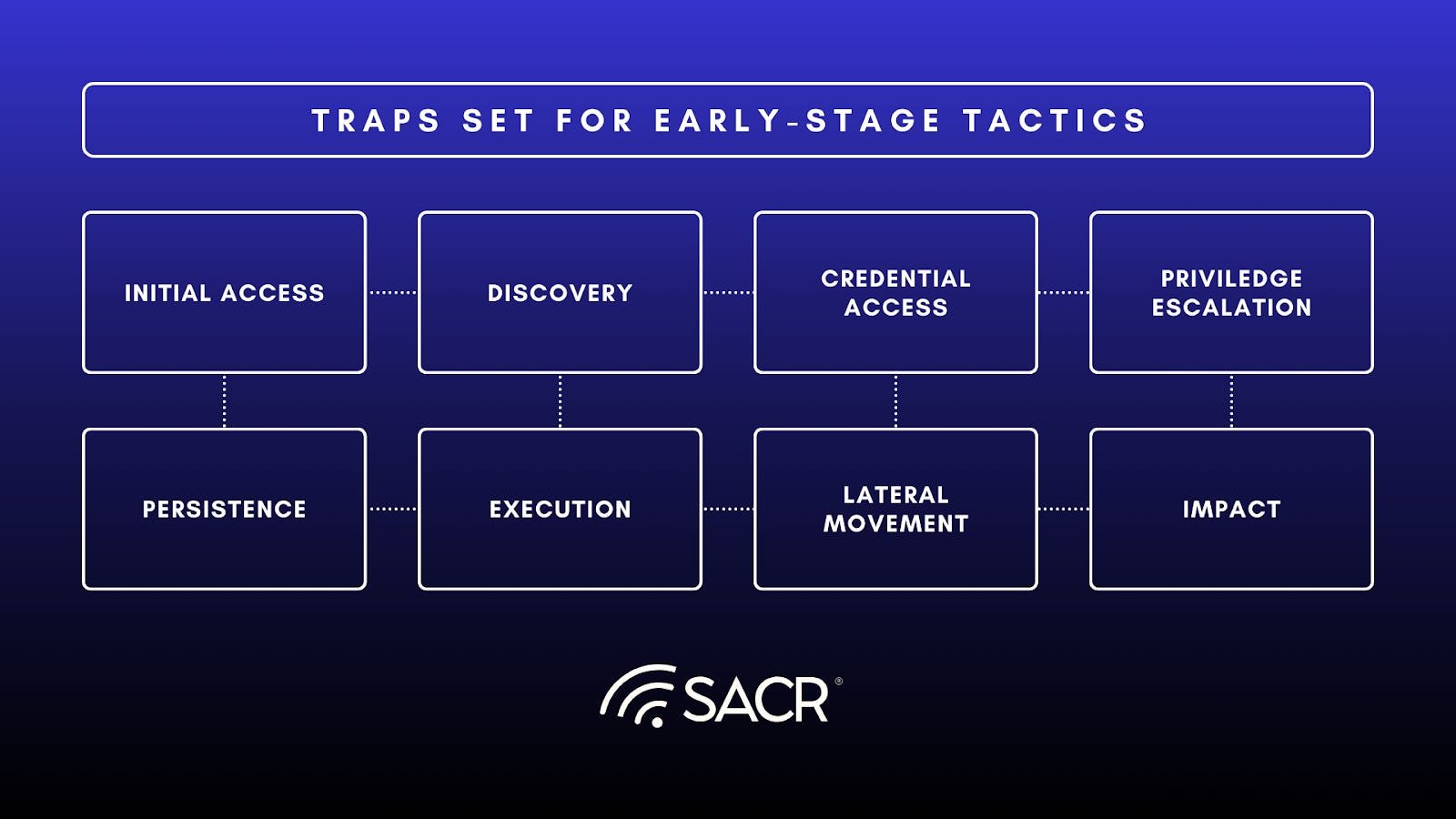
Actionable Summary This report analyzes the emergence of Preemptive Deception Platform and Acalvio’s market position, technical differentiation, and value proposition.
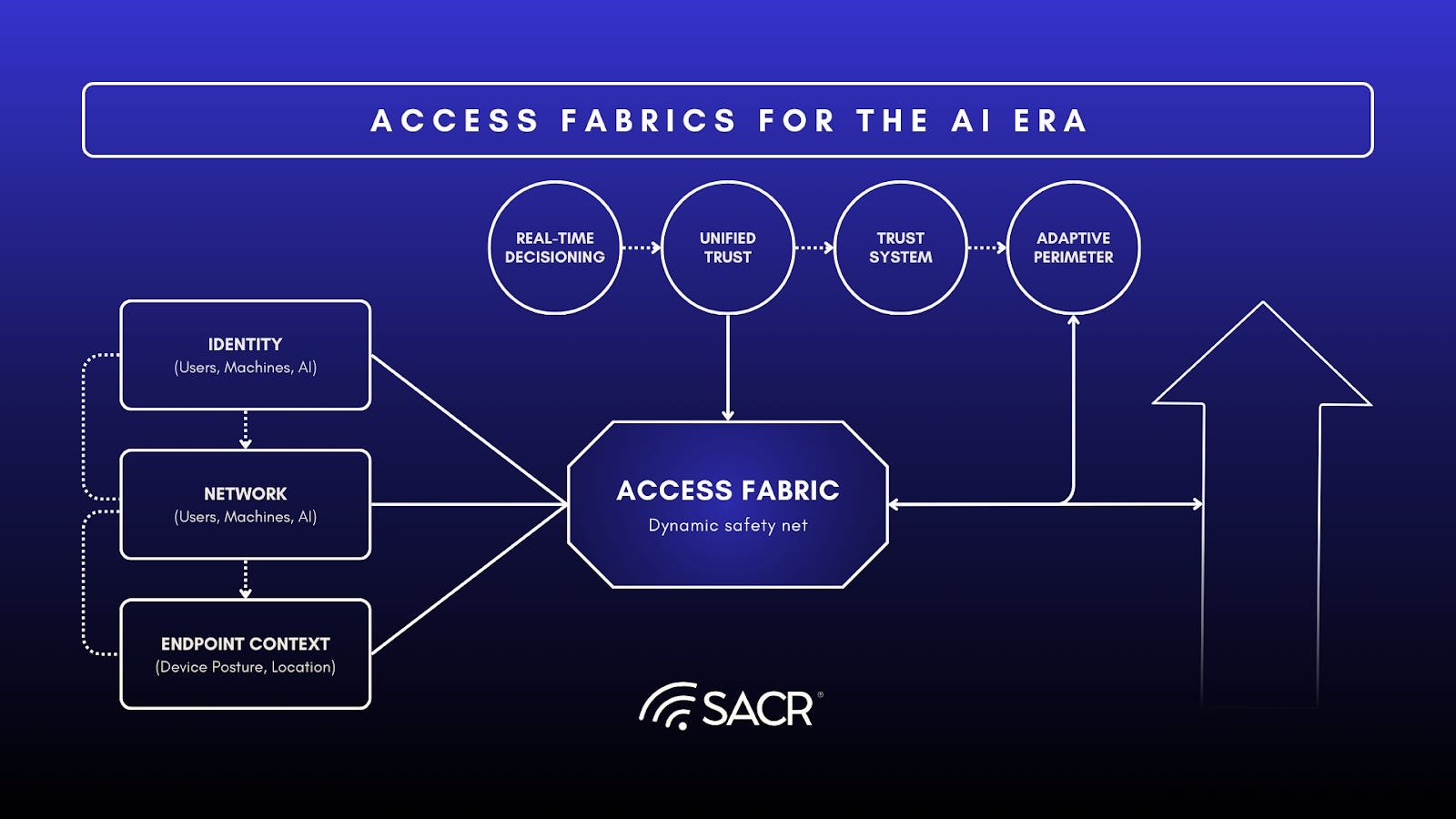
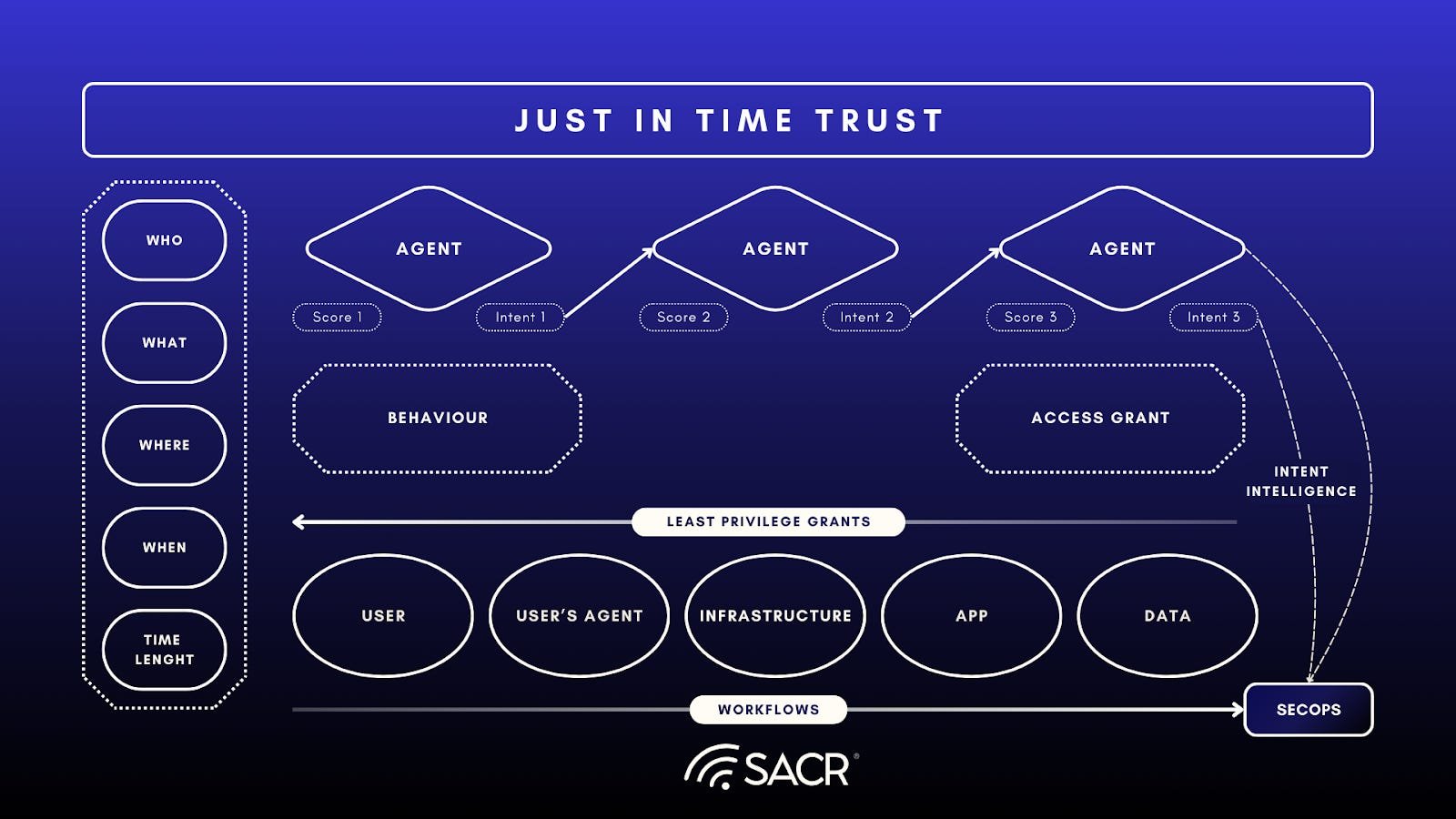
Executive Summary The cybersecurity landscape is shifting from securing perimeters to securing transactions. While Zero Trust provides the necessary philosophy,
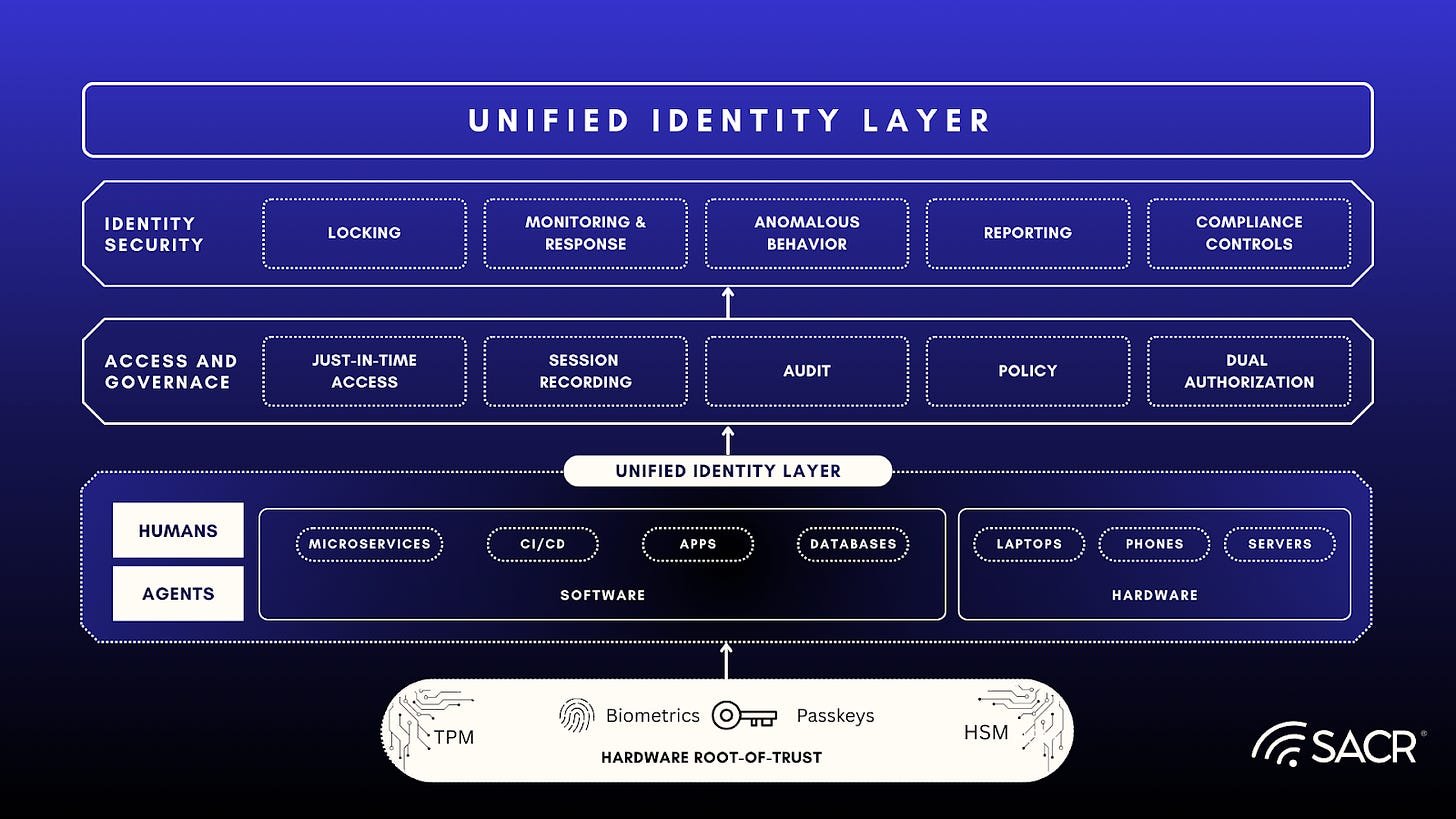
Executive Summary Security practitioners need to prioritize a fundamental reimagining of Privileged Access Management (PAM) and Identity Security, focusing on
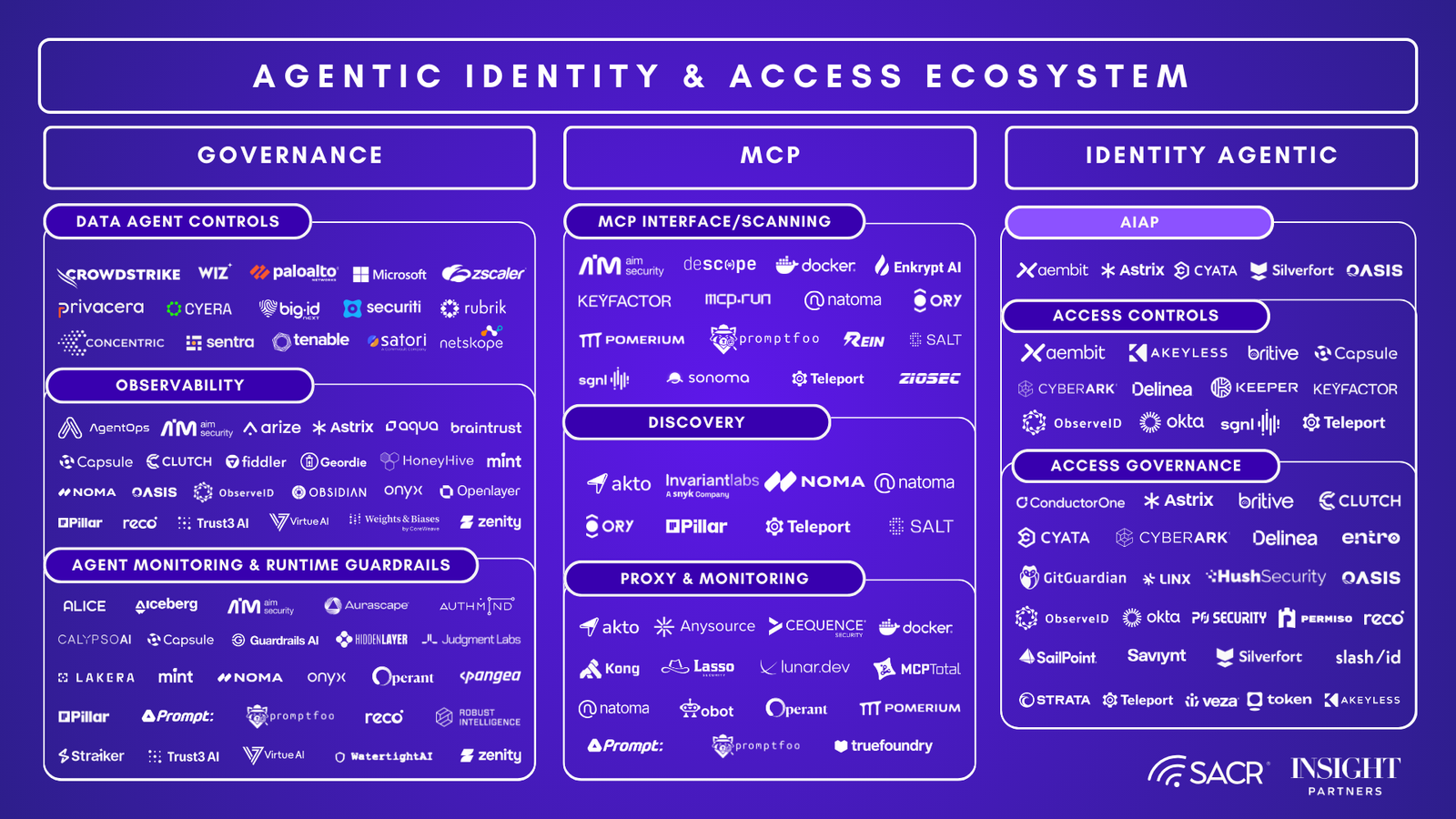
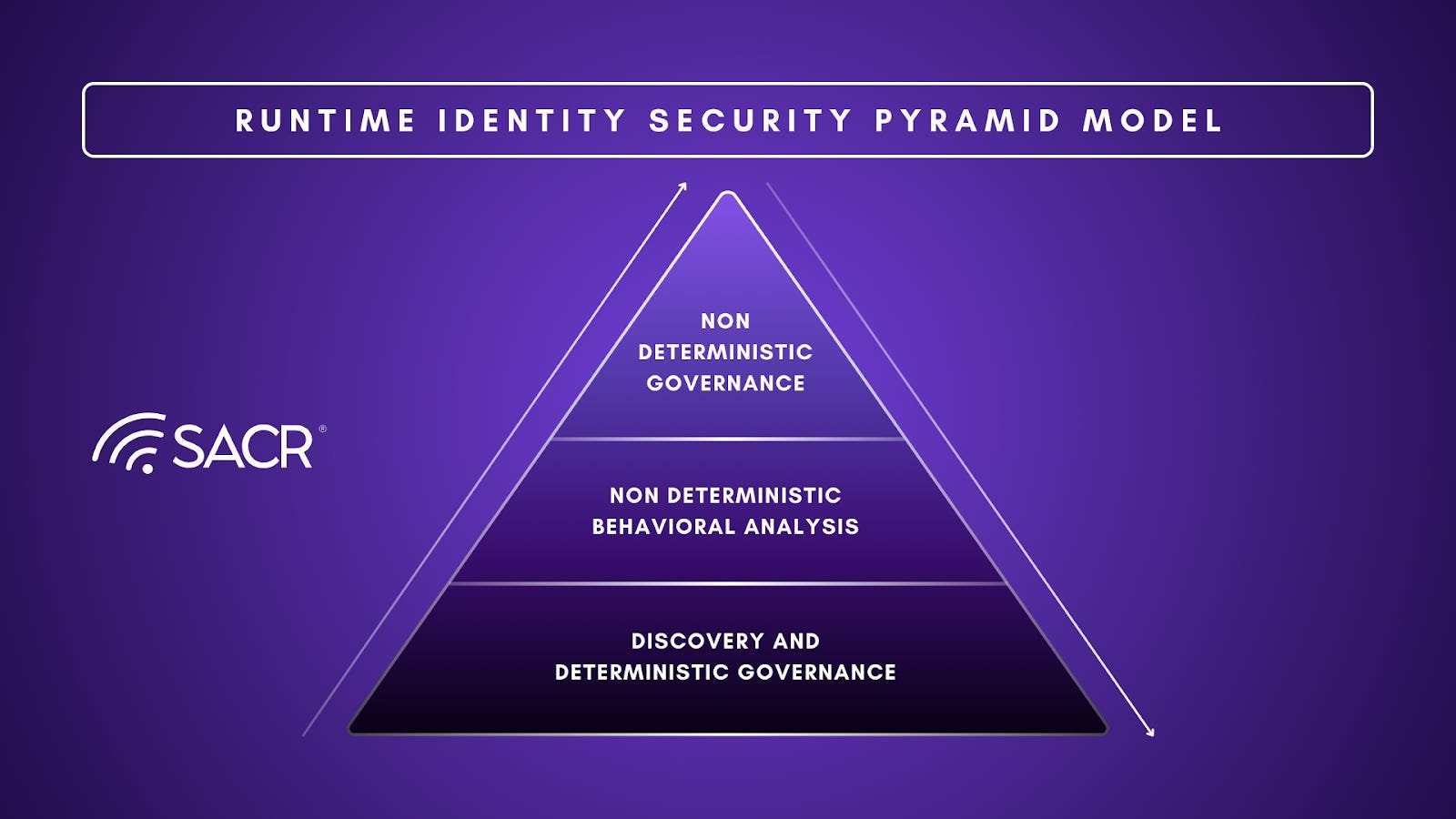
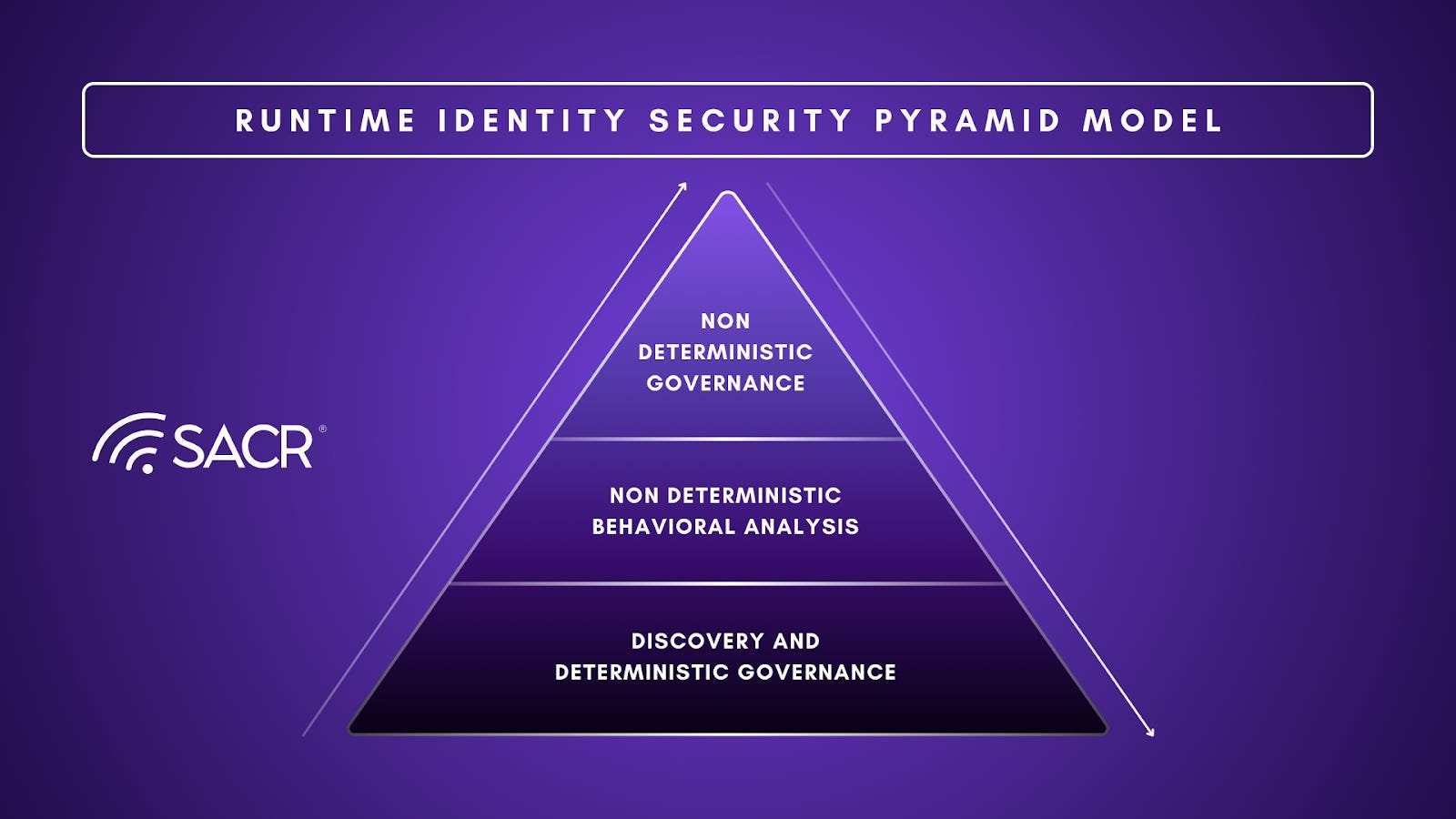
Executive summary SACR is betting that Identity security will change significantly in 2026, shifting from how IAM / Security leaders have
Author Lawrence Pingree is the Head of Data and AI Security at SACR, where he leads research on data protection,
Subscribe for a weekly digest on the best private technology companies.