Executive Summary
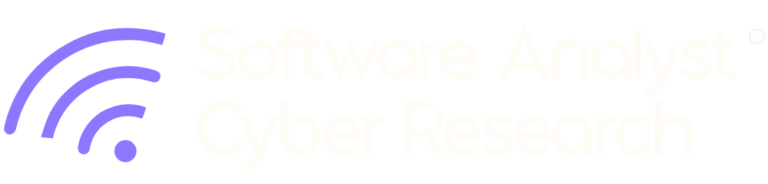
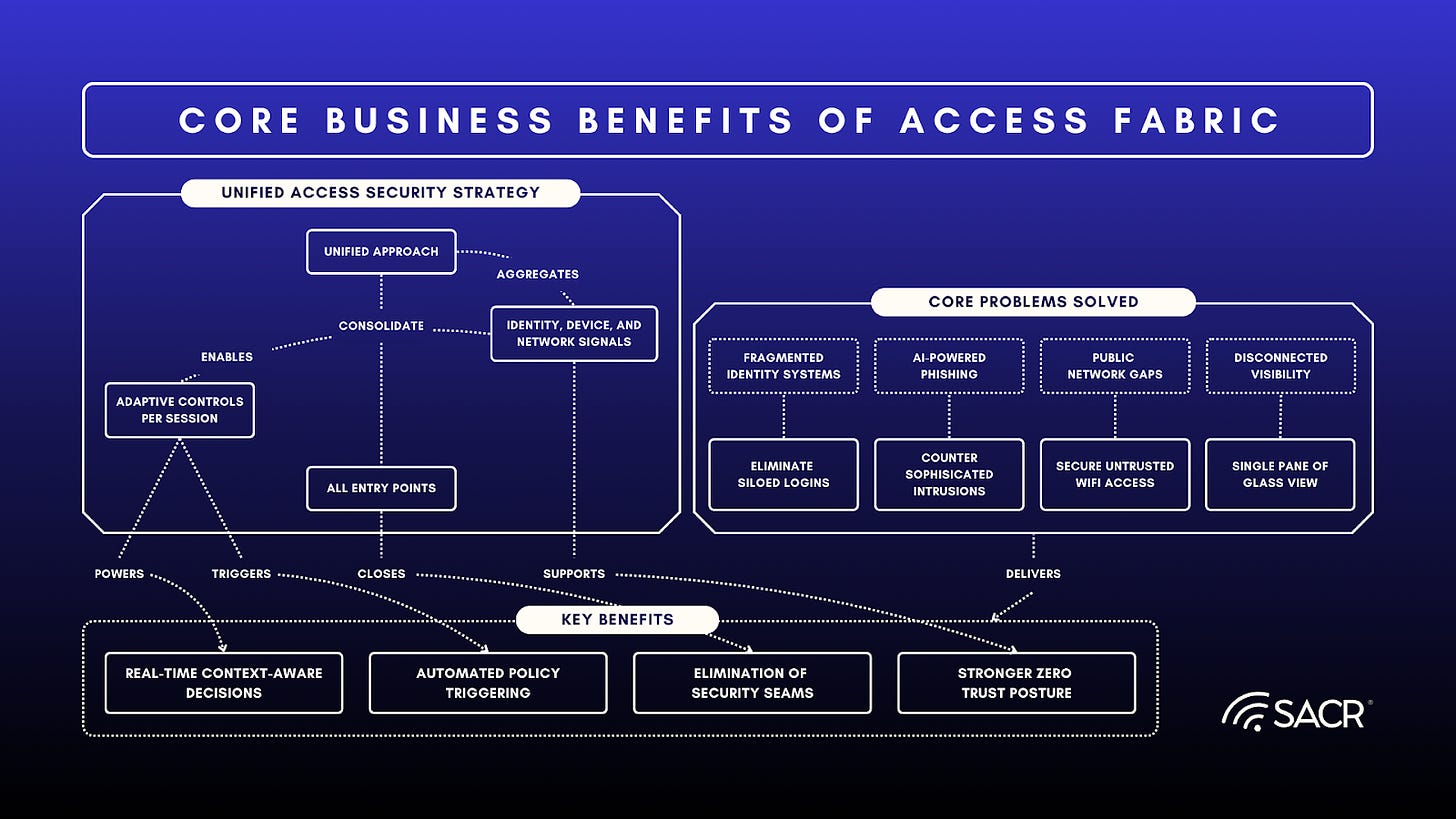
The cybersecurity landscape is shifting from securing perimeters to securing transactions. While Zero Trust provides the necessary philosophy, Never trust, always verify, organizations often struggle with its technical implementation due to siloed security stacks, disconnected events, a lack of unified context, and a misunderstanding of intent. This fragmentation leads to inefficient use of scarce security resources, worse end user experience and ultimately, poorer security with blind spots.. In the age of AI, this fragmentation of identities and access is the root cause of exploitation and weaknesses in tool use, data access, and the execution of workflows with authenticity.
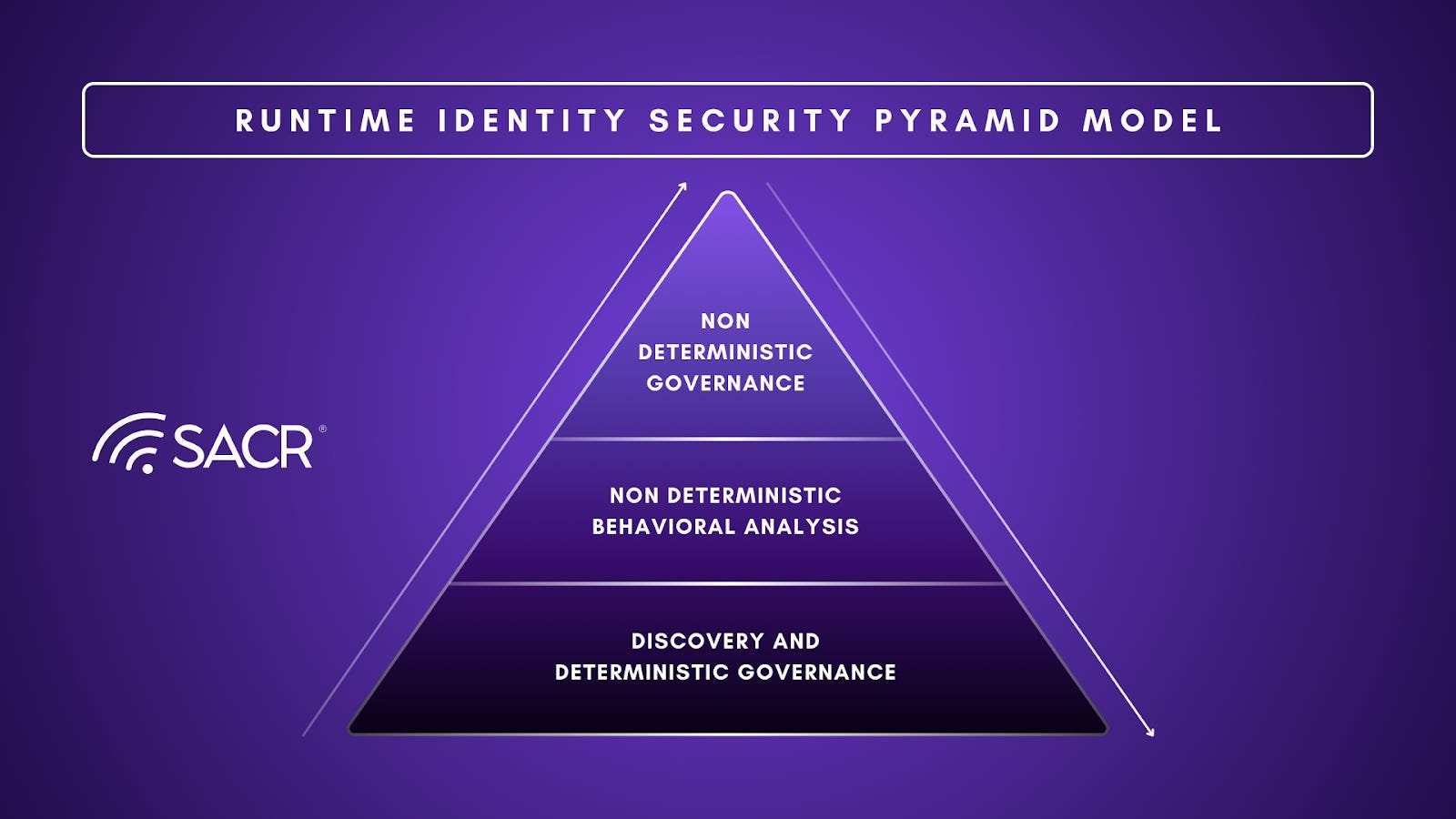
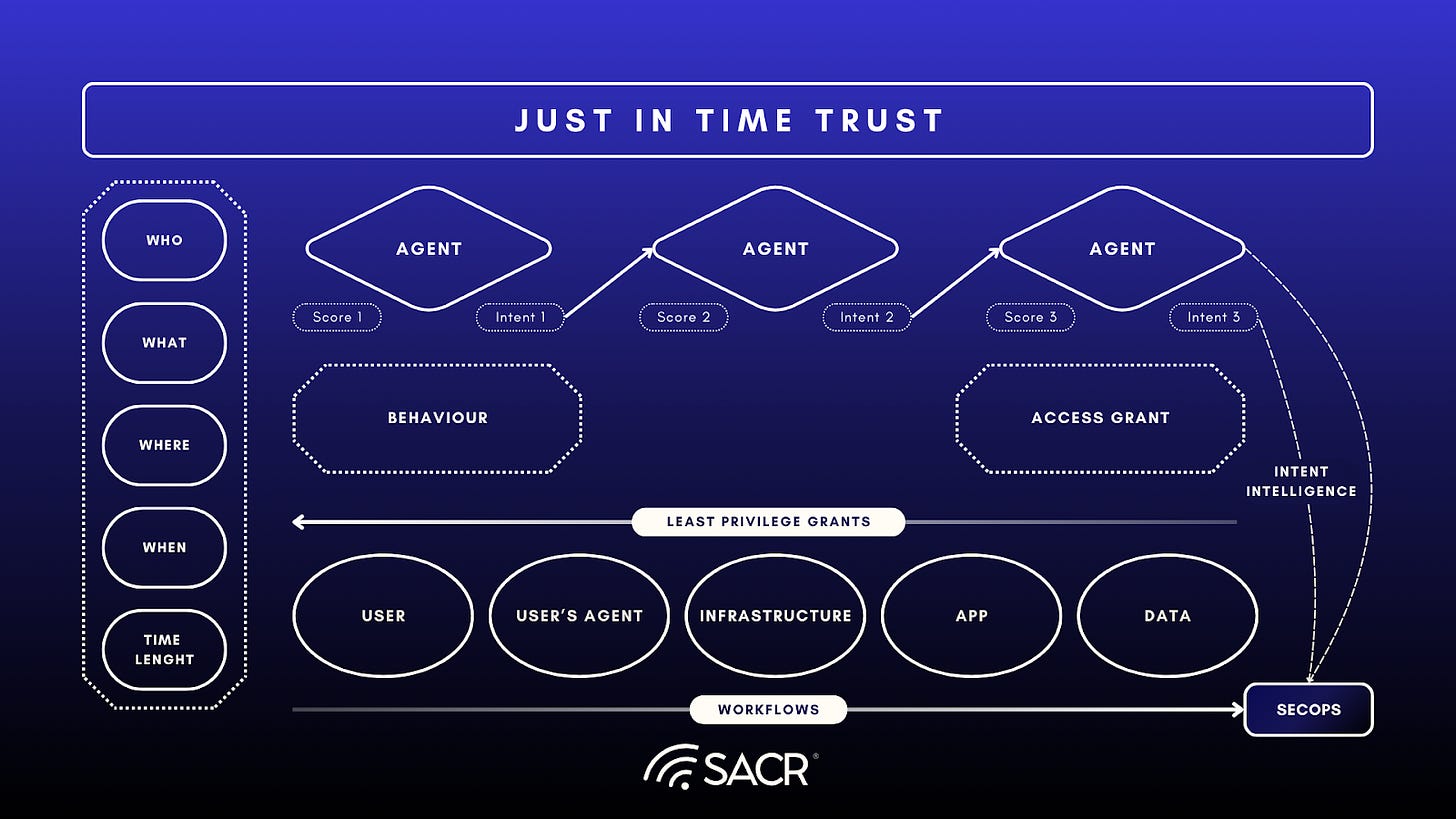
This report introduces and synthesizes the emergence of the Access Fabric concept, built on the thesis that intent will be a much better predictor of behavioral assessment than traditional scoring of various events independently. An Access Fabric is not a single product but an architectural and behavioral paradigm that moves beyond Zero Trust into Just-in-Time Trust concepts. It is an interconnected mesh of security services that continuously exchange signals, unify context, and enforce policy dynamically.
The core principles critical for the establishment of an Access Fabric are:
Continuous: It is a real-time, dynamic safety net that continuously verifies trust during every session. It is designed to apply to all identities (human and non-human) and is intended to help drive the market toward a dynamic defense by coordinating signals to make correlated decisions.
Intent Awareness: Using innovations from Large Language Models (LLMs) to derive continuous behavioral Intent, monitored over time to detect behavioral drift into malicious behavior.
Contextual: It applies contextual intelligence, integrating signals from various security components (such as a Security Service Edge, Data Governance system, and Identity Platform) to assess the trustworthiness of any interaction, with “intent” being a component of context.
Converged: It aims to integrate identity and network controls into a single, unified policy management framework to ensure consistent policies across apps, endpoints, and network edges.
The Industry Challenge
The current state of cybersecurity is challenged by several fundamental flaws that prevent organizations from fully realizing the potential of a Zero Trust model, particularly as non-human identities and AI-driven threats become more prevalent. These problems stem primarily from an architecture of disconnected tools and services.
The primary issue is the fragmentation of the security ecosystem. Organizations typically operate with siloed security stacks, where different tools handle separate domains (e.g., one system for network security, another for identity authentication). This results in:
- Disconnected Events and Context Gaps: Security events are not correlated in real-time. For example, if a network service detects suspicious behavior after a user has already authenticated, that context is not immediately available to the Identity Provider to revoke access. This latency and lack of unified context create a critical window for attackers to exploit.
- Poor Behavioral Monitoring: The fragmentation leads to a disjointed security narrative, making it difficult to establish a consistent baseline for normal behavior. Without a unified view, the subtle behavioral drift indicative of a sophisticated threat is often missed, leading to false positives and an inability to properly monitor human and non-human activities.
- Misunderstanding of Intent: Current systems largely focus on scoring independent events, failing to assess the continuous, evolving “intent” behind a user’s or AI agent’s actions. This lack of intent awareness is a major weakness against advanced persistent threats.
This research highlights that in the age of generative AI, architectural fragmentation has become the root cause of exploitation.
- Weaknesses in AI Workflow: The division of identities and access controls makes it difficult to govern the new class of non-human Agentics (AI agents). Their access to tools, data, and the execution of workflows lack the required authenticity and continuous verification.
- Exploitation of Identity Silos: The cybersecurity landscape’s fragmentation of identities and access is directly leveraged by attackers, making the complex, multi-layered environment the source of security weaknesses.
How does an Access Fabric Address the Access Challenge?
The Access Fabric is not a single product but a composable, identity-centric architectural layer that weaves together identity, network, and endpoint context to create a dynamic safety net around every digital interaction. It replaces the static, rigid network perimeter with a lattice of real-time decisions, ensuring that only the right entities (humans, machines, or AI agents) access the right resources under the right conditions. This representation uplifts current cybersecurity by shifting from disconnected point tools to a unified living system of trust.
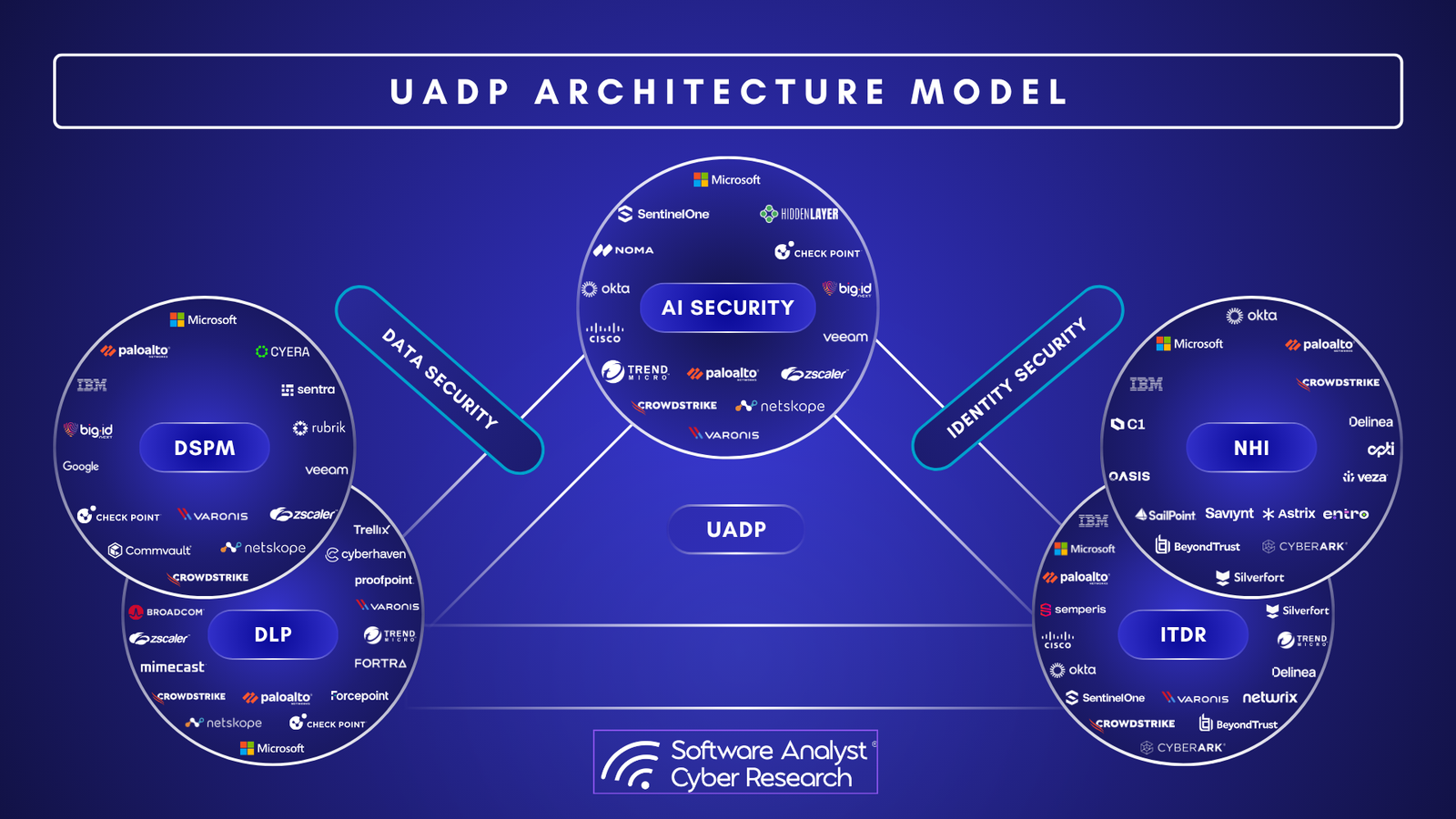
Central to this concept is an Access Graph. This architectural component acts as a unified intelligence engine, aggregating data across the security ecosystem. The Access Fabric moves beyond static policy integration to a state of continuous, interdependent risk evaluation for all identities and transactions. It addresses key challenges in access governance, risk and authorization. It delivers automatic protection for common attack vectors, elimination of manual integration/silos, and real-time adaptive controls for AI and SaaS applications.
The Imperative for a Fabric Approach
Current security architectures are often disjointed. A Security Service Edge (SSE) solution might secure the network edge, while an Identity Provider (IdP) handles authentication. However, if the network sees suspicious behavior afterauthentication, that context is not always immediately available to the IdP or shared among federation providers to properly revoke access in real-time. This latency and context gap is the fundamental flaw of identity-centric models that do not extend into continuous runtime access control.
An Access Fabric addresses this gap. It weaves together disparate security domains into a cohesive whole, ensuring that a signal generated in one domain (e.g., a data exfiltration attempt detected by a Data Governance solution) instantaneously affects policy enforcement across all others (e.g., stepping up authentication in the IdP or blocking network access via the SSE), Unifying Human and Non-Human Identity.
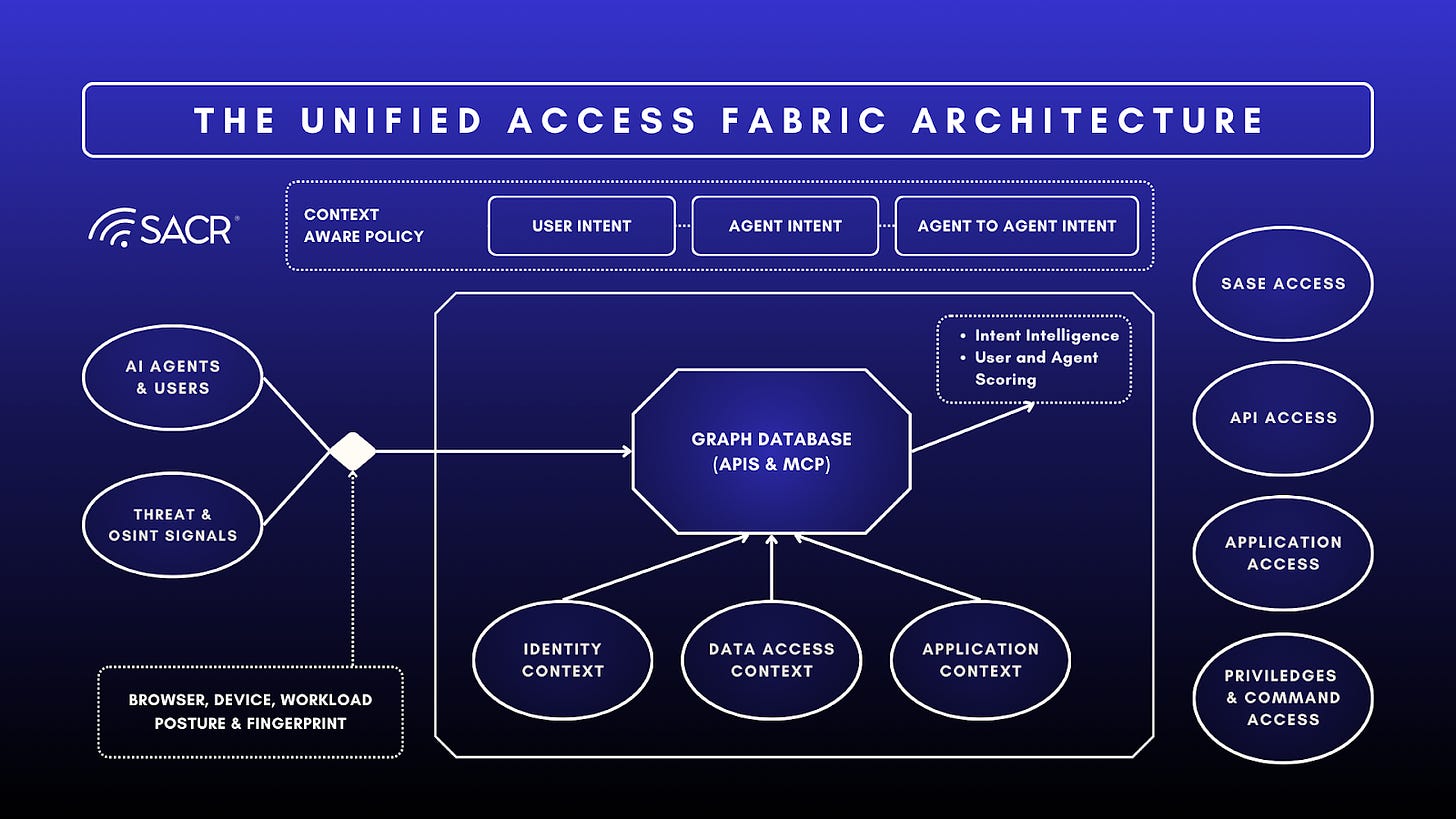
The rise of generative AI introduces a critical new class of identities: non-human Agentics (AI agents). The Access Fabric is designed from the ground up to govern machine-to-machine and human-to-machine interactions with the same rigor as human-to-resource access. Access control is unified across all identity types, treating them as first-class citizens in a zero-trust model.
- Continuous Verification for Agents: AI agents, particularly those operating within productivity environments (e.g., accessing shared drives or triggering workflows), become new endpoints that require continuous verification, not just static API keys. The Fabric enforces this by treating each agent’s execution or API call as a transaction requiring a real-time Access Score from the Access Graph or of the user actor and the various things they are accessing.
- Behavioral Intent for Agents: The Large Language Model (LLM) capabilities that derive human behavioral intent must also be applied to AI agents. The Access Graph monitors agentic workflows and data usage patterns to detect behavioral drift, such as an agent attempting to download an unusually large volume of highly confidential data, flagging this as potential malicious or poor behavior.
- Integrated Context: The Access Fabric leverages an Intelligence Graph to aggregate context about the agent’s actions, the sensitivity of the data it is accessing (from a Data Governance system), and the resource and network it is operating on. This integrated context allows for dynamic enforcement actions.
The Central Nervous System: The Intent-Aware Access Graph
At the heart of the Access Fabric lies the emerging Intent Awareness in the Access Graph. If the Fabric is the body, the Graph is the central nervous system, and intent is the intelligent, LLM-based prediction of outcomes. The Access Graph is not merely a data repository; it is a dynamic processing hub that ingests raw signals and outputs actionable intelligence across security controls, creating a weaved response to a potential risk or threat, or emerging malicious intent.
The Access Fabric diagram illustrates bidirectional data flows (double-sided arrows) between the peripheral services and the Graph. This indicates a continuous loop where services both feed context into the Graph to update scores and consume the aggregated scores and a judgment by a behavioral LLM on the intent to make enforcement decisions simultaneously.
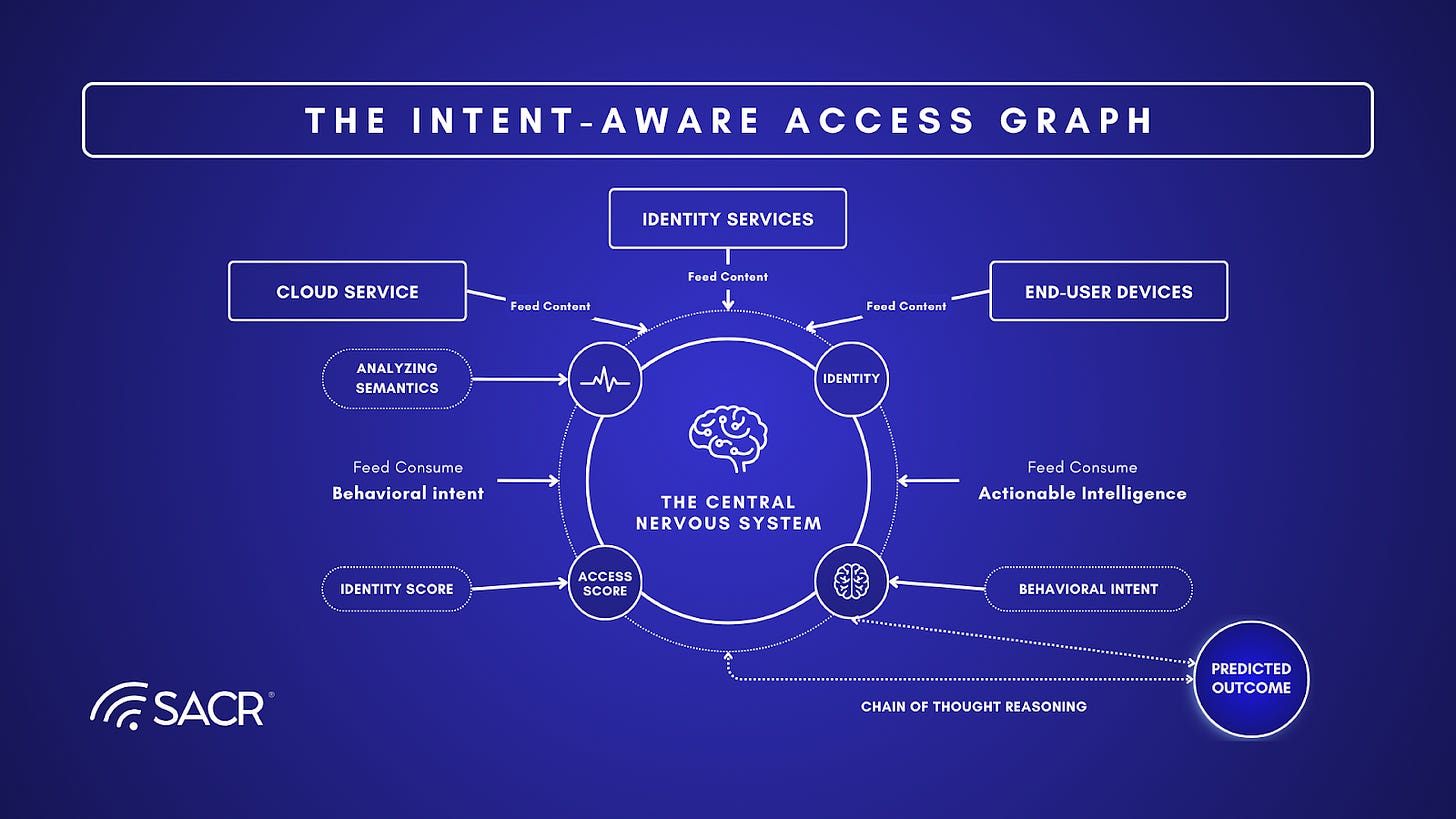
The core functions of the Access Graph are to compute and maintain:
- Risk Profile: An aggregated view of the current threat level associated with an entity.
- User/Identity Score: A dynamic metric reflecting the behavioral trustworthiness of an identity (human or non-human).
- Access Score: A real-time evaluation of the specific request’s risk based on context (device, location, resource sensitivity).
- Behavioral Intent: The prediction or inference of an identity’s likely future action or goal, drawn from the analysis of their textual input or chain of thought (CoT) reasoning.
- Semantics: LLMs analyze the semantics, context, tone, and typical linguistic patterns associated with various actions to identify the underlying motivation or desired outcome.
For example, an LLM AI model can perform a best estimate of:
- What is this user trying to do next?
- What is the ultimate purpose behind this communication?
- Is this prediction malicious, poor behavior, or normal work?
- Agent or multi-agent reasoning: For instance, if an agent’s internal CoT is monitored and it thinks to itself “ I think accessing the corporate hr database would be a good source of data.” (CoT reasoning)
Core Architectural Layers of an Access Fabric
An access fabric can be visualized as four interoperable layers that function continuously during every session, rather than just at the initial login. Various tools mentioned throughout this note map to the functions within these generic layers.
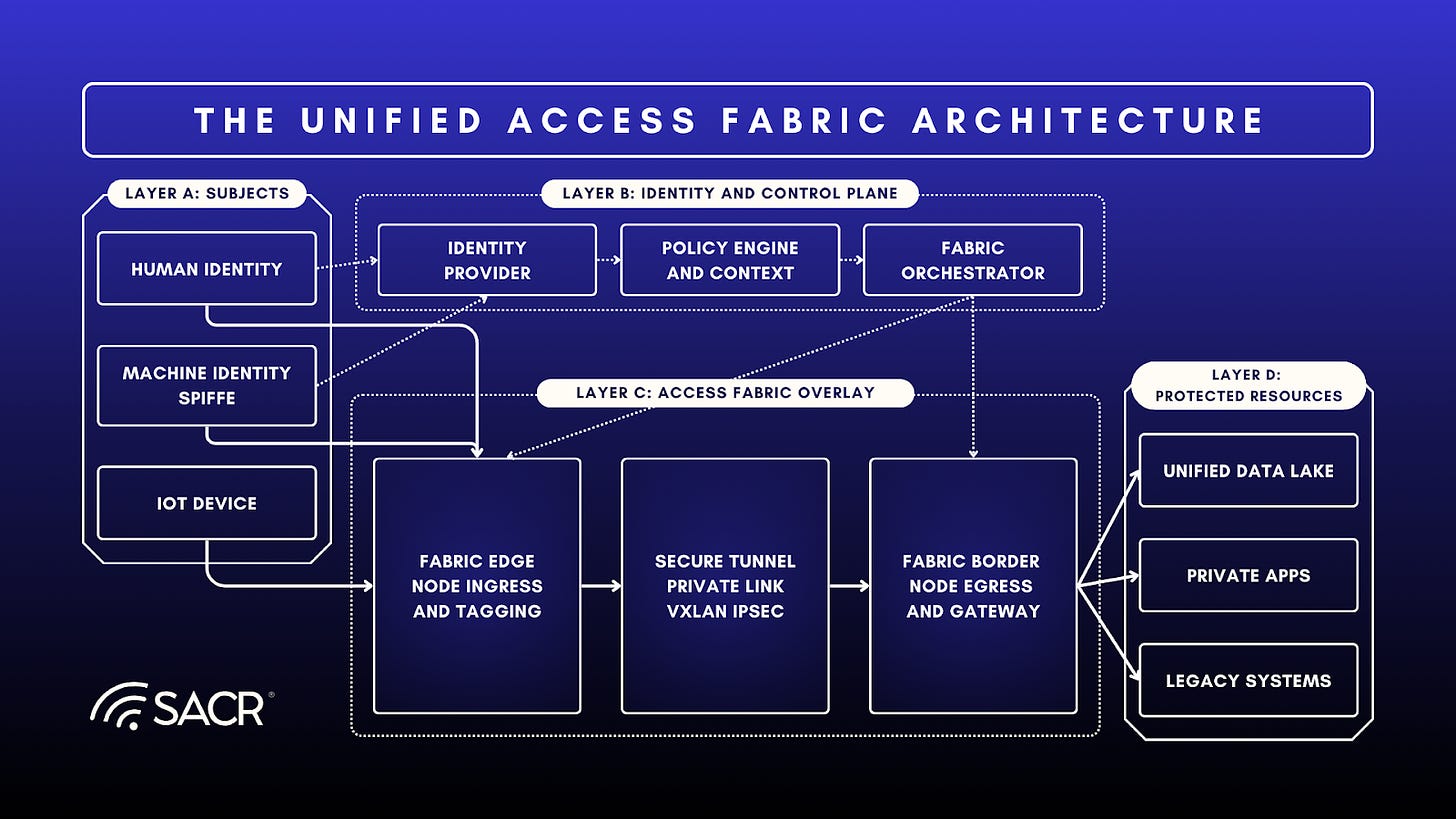
Layer A: The Identity & Context Plane (The Subject)
Function: Unifies the definition of who or what is requesting access. It moves beyond simple username/password to a rich, multidimensional identity profile.
The customer value of Layer A, the Identity & Context Plane, is foundational security and simplified visibility. By creating a Unified Identity Directory for all entities, humans, machines, and the exponentially growing number of AI agents, it provides a single source of truth for access decisions. This eliminates the blind spots and security weaknesses inherent in managing multiple, siloed identity stores. Customers gain immediate value by dramatically improving their risk posture, ensuring that access is always granted to a fully attested, multi-dimensional identity (Layer B’s Subject) based on a comprehensive profile that includes not just who they are, but where they are and what their device health is. This unification is the critical first step in achieving truly comprehensive Zero Trust, as it standardizes the input for continuous trust evaluation across the entire enterprise.
Layer A Components:
- Unified Identity Directory: Aggregates human identities (employees, partners) and Non-Human Identities (NHIs) (service accounts, bots, AI agents), which often outnumber humans 50:1. (Maps to The Identity Pillar)
- Contextual Signals: Continuously ingests telemetry regarding device health, location, network risk, and user behavior. (Maps to signals from The Network Pillar / Access, The Data Pillar, and The Endpoint Pillar)
- Workload Attestation: Uses frameworks like SPIFFE to issue cryptographically verifiable identities to software workloads at runtime based on environmental attributes (e.g., container image hash, kernel metadata) rather than static secrets.
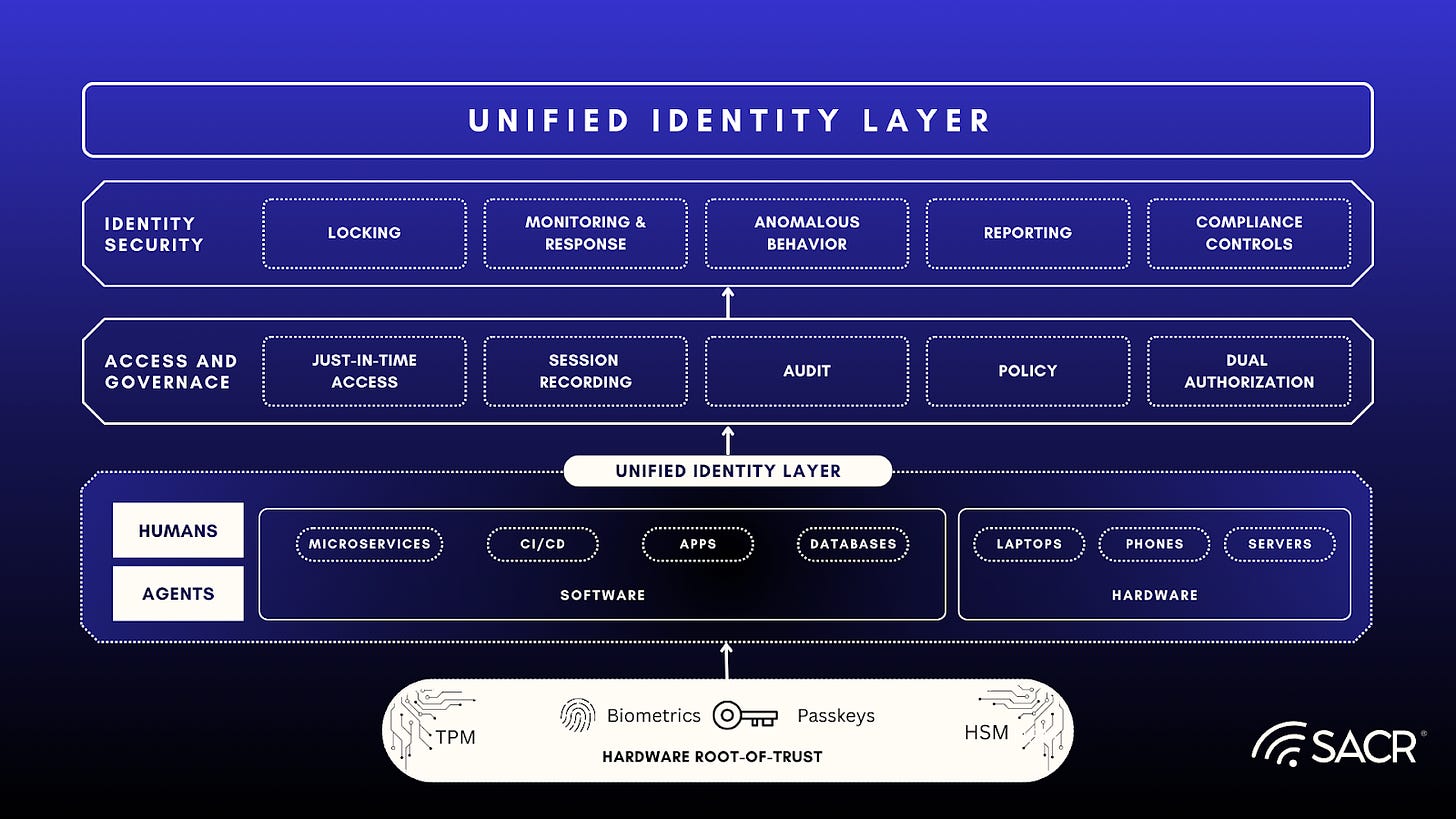
Layer B: The Intelligence & Policy Plane (The Brain)
Function: The central decision engine that evaluates trust in real-time. It operationalizes Zero Trust principles (”never trust, always verify”) by continuously re-evaluating risk throughout a session.
For organizations, the Access Fabric (Layer B) provides a unified, intelligent foundation for Zero Trust. It eliminates siloed access tools, reducing complexity and operational overhead. This single control layer accelerates the deployment of new services and applications while ensuring consistent, high-fidelity risk assessment for every transaction. The result is a more secure, future-ready infrastructure that maximizes IT and security team efficiency.
Layer B Components:
- AI-Driven Risk Engine: Uses machine learning to detect anomalies and assigns dynamic risk scores. (Maps directly to the Access Graph‘s core function).
- Unified Policy Management: A central control plane where security teams define consistent rules that apply across clouds, on-premises, and SaaS, preventing policy fragmentation.
- Security Intelligence: Normalizes and correlates signals from disparate tools to identify complex threat patterns. (Maps to the correlative function of the Access Graph and the analysis capabilities of The Operations Pillar).
Layer C: The Orchestration & Interoperability Plane (The Weave)
Function: The connective tissue that ensures disparate systems (legacy apps, modern clouds, third-party IDPs) can communicate and enforce the decisions made by the Policy Plane.
For the security and IT operator, Layer C, the Orchestration & Interoperability Plane, delivers essential business continuity and operational flexibility. Its primary value is the elimination of technology debt as a barrier to modern security adoption. By acting as a universal translator, it allows organizations to extend the Zero Trust principles of the Access Fabric to all their assets, modern cloud services and mission-critical legacy applications alike, without undertaking costly, high-risk, multi-year code modernization projects. This results in faster time-to-value for the entire Access Fabric deployment, reduced system brittleness, and the ability to maintain consistent security policy enforcement across a heterogeneous, hybrid IT environment.
Layer C Components:
- Identity Orchestration: Bridges fragmented identity systems (e.g., merging Okta, Microsoft Entra, and legacy LDAP) without requiring code rewrites.
- Standardized Interoperability: Relies on protocols like OAuth 2.0, OIDC, SAML, and SCIM to ensure data flows meaningfully between systems.
- Translation Layers: Converts modern authentication (e.g., passwordless, MFA) into formats that legacy applications can understand, extending the fabric to older infrastructure.
Layer D: The Enforcement & Connectivity Plane (The Edge)
Function: The execution arm that grants or blocks access at the data path level. It ensures no user connects to a network, only to specific applications (Universal ZTNA).
The Enforcement & Connectivity Plane (Layer D) provides tangible, immediate value to customers by acting as the ultimate shield against modern network threats. Its primary value is the implementation of Universal ZTNA (Zero Trust Network Access), which eliminates the legacy (always on and trusted) connection to the network vulnerability. By ensuring that every request is a direct, isolated connection to a specific application or resource, Layer D eradicates the possibility of lateral movement or unauthorized network scanning, even if an attacker compromises a credential. This layer delivers a least-privilege-by-default posture that is effortless for the user and comprehensive in its coverage, reducing the attack surface by making assets invisible to unauthorized parties and helps avoid the use of identity dark matter, thereby providing the highest degree of confidence in the integrity of every transaction.
Layer D Components:
- Identity-Aware Proxies (IAP): Sits in front of resources, requiring authentication before the resource is even visible (identity dark matter assets).
- Micro-Segmentation Gateways: Enforces least-privilege access, ensuring a camera cannot talk to an HR database or a user cannot move laterally after a breach. (Maps to enforcement actions by The Network Pillar / SASE Access and The Endpoint Pillar).
- Service Proxies (e.g., Envoy): Manages secure mTLS communication between microservices, rotating short-lived certificates automatically.
Uplifting Current Cybersecurity Concepts
The Access Fabric model improves upon traditional security concepts in three critical ways:
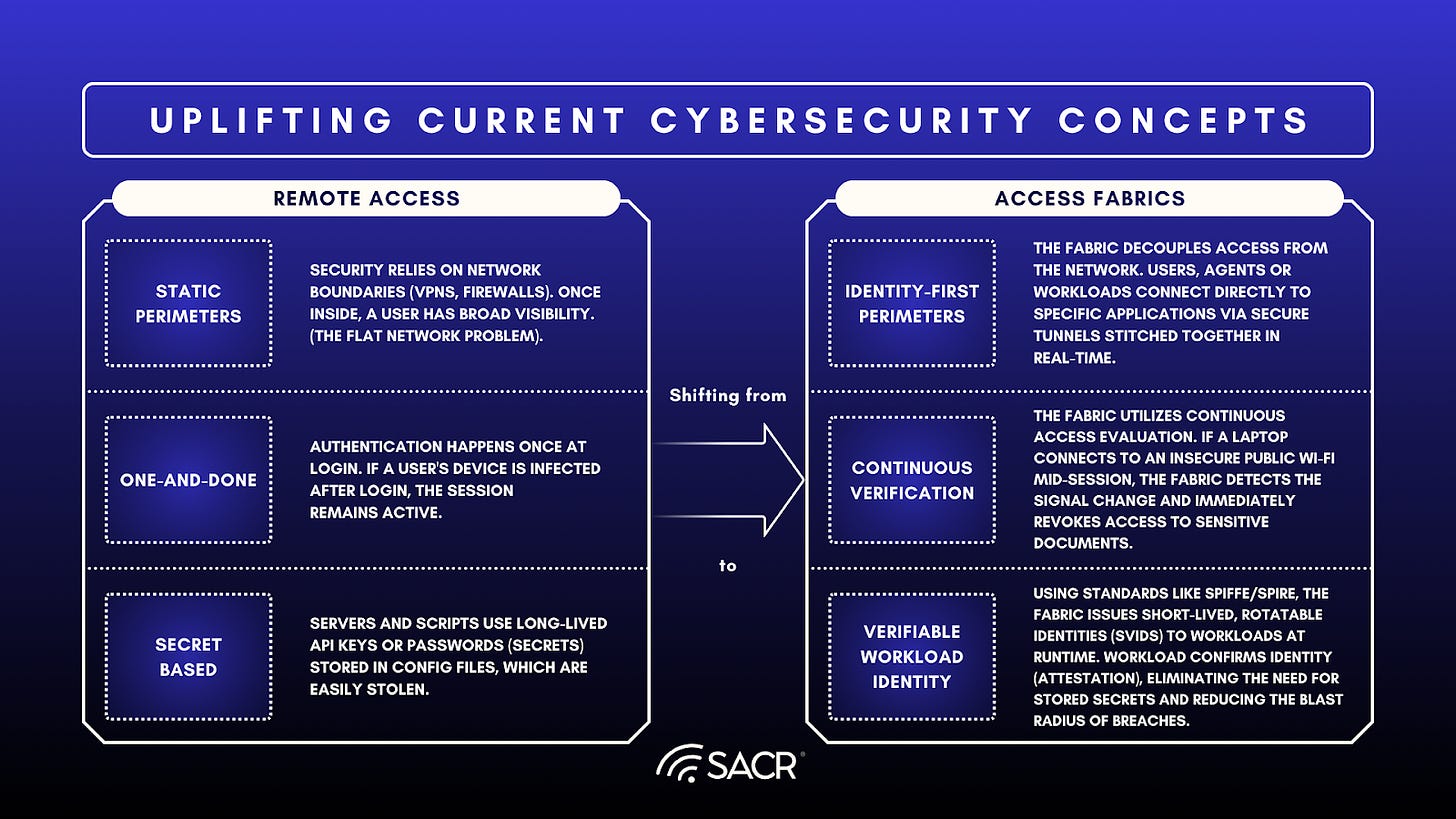
From Static Perimeters to Identity-First Perimeters:
- Current Concept: Security relies on network boundaries (VPNs, Firewalls). Once inside, a user has broad visibility (the flat network problem).
- Fabric Uplift: The fabric decouples access from the network. Users/Workloads connect directly to specific applications via secure tunnels stitched together in real-time. The perimeter follows the identity, whether on-prem, at a coffee shop, or in the cloud.
From One-and-Done to Continuous Verification:
- Current Concept: Authentication happens once at login. If a user’s device is infected after login, the session remains active.
- Fabric Uplift: The fabric utilizes Continuous Access Evaluation. If a laptop connects to an insecure public Wi-Fi mid-session, the fabric detects the signal change and immediately revokes access to sensitive documents.
From Secret-Based to Verifiable Workload Identity:
- Current Concept: Servers and scripts use long-lived API keys or passwords (secrets) stored in config files, which are easily stolen.
- Fabric Uplift: Using standards like SPIFFE/SPIRE, the fabric issues short-lived, rotatable identities (SVIDs) designed for run-time, A2A and MCP flows while also supporting user-on-behalf-of concepts for workloads at runtime. A workload proves what it is (attestation) to get an identity, eliminating the need for stored secrets and reducing the blast radius of breaches.
Business & Operational Value
- Security Resilience: By closing the gaps between fragmented tools, the fabric reduces the seams that attackers exploit. Organizations using such mesh architectures can reduce the financial impact of incidents by 90%.
- Operational Efficiency: It centralizes governance. Policies are set once and applied everywhere, reducing the complexity of managing dozens of admin consoles.
- Legacy Modernization: It allows organizations to wrap legacy applications in modern security (MFA, SSO) without rewriting code, extending the life and security of critical vintage assets.
The Emerging Threat Pillars: Behavioral Intent & Agentics
The integration highlights forward-looking inputs:
- Behavioral Intent / Preemptive Indicators: The analysis of Preemptive Indicators of Intent and Behavior (PIIB) determines malicious, business as usual, and actualized intent. This moves security from reactive to predictive, feeding preemptive risk signals into the Fabric before an attack executes.
- Agentics & API Access: The inclusion of Agentics (a.k.a AI agents) and API Access (non-human identities) acknowledges that the modern Access Fabric must govern machine-to-machine interactions with the same rigor as human access, using specific contexts like Automation Device/IP.
- JIT-Trust Capable: Future Access Fabrics must be Just in Time Trust (JIT-TRUST) capable systems, evaluating intent intelligence from user to chat, agent to agent and chain of thought (CoT) aware and connected to various sandbox runtime telemetry to enhance trust based on behavior.
A Day in the Life: Elara and the Access Fabric
6:30 AM – Smooth Sailing to Start
Elara, a product manager at a huge global tech company, wakes up. Her smart home hub, basically a personal AI buddy plugged into the Access Fabric, spots her biometrics and sees she’s near her main work device (a cool, foldable display). The Fabric, which is this underlying, super-smart security and connection layer, immediately fires up a personalized, high-speed contextual channel just for her.
How it Works: The home hub (a device agent) confirms Elara’s identity using biometrics, and the Fabric’s rules engine gives it exactly the access it needs, right when it needs it (just-in-time access) to her home network and news feeds. No passwords required! The Fabric uses a distributed ledger to double-check the device’s security and Elara’s identity against her official corporate file.
8:00 AM – On the Road, No Dropped Calls
Elara hops into her self-driving car. As her phone links up, the Fabric handles a perfect contextual hand-off. That video call with her Shanghai team? It jumps straight from her home display to the car’s heads-up display without a hiccup. Her cloud-based VDI (virtual desktop), running in a super-secure bubble, automatically cranks up its bandwidth because the Fabric senses the car’s solid connection and location.
How it Works: The car and the phone are both like Elara’s proxies (device agents). The Fabric slaps the company’s Zero Trust policy on them: it trusts the car system only for the ride, letting it access the VDI’s audio/video stream but blocking any data downloads. Meanwhile, her personal AI assistant (a software agent) catches her up on yesterday’s meeting notes through the car speakers.
10:00 AM – Design Review Time
Elara walks into the conference room. Proximity sensors powered by the Fabric recognize her and automatically connect her to the scheduled meeting display. She pulls up a confidential design doc. Mark, a third-party contractor, joins remotely.
How it Works: The Fabric’s identity system (IAM) is totally integrated. Elara gets full edit rights (high access). Mark’s access, set by the Fabric’s policy engine, is dynamically restricted to view-only for the sensitive parts of the document, and he can only share approved applications on his screen. If Mark tries to sneak a screenshot of the confidential stuff, the Fabric’s real-time data loss prevention (DLP) agent blocks it and logs the attempted breach.
1:00 PM – Lunch Break Surprise
During lunch, Elara gets an urgent alert: a critical sensor at a remote site is acting up. She has to grant a specialized diagnostic AI agent temporary access to the facility’s control system.
How it Works: Elara (the user) tells her personal AI (her agent) to request access for the diagnostic AI (another agent). The Fabric’s access broker checks the company rules, which require multi-level sign-off for infrastructure access. Since Elara is authorized, she just uses a quick, one-time biometric scan on her phone. The Fabric then creates a micro-segment, which employs a tiny, secure tunnel, straight between the diagnostic AI’s isolated environment and the sensor’s specific API. This grants it only read/write access to the diagnostic port, and only for a maximum of 30 minutes. The rest of the network is totally safe.
3:30 PM – Teamwork with an External Partner
Elara is working with an outside partner on a joint development project, using a shared, encrypted workspace.
How it Works: The Fabric sees the external partner as an unmanaged external agent. The Fabric’s rules ensure that any data going from Elara’s work device to the shared workspace is automatically turned into a token and encrypted using a key they both manage. The Fabric keeps a complete, tamper-proof record of every interaction (an immutable audit trail), making sure the company stays compliant without slowing down collaboration. The ever-present AI agent on the Fabric spots a potential IP issue by comparing the partner’s code to Elara’s company’s patents, automatically flagging it for a legal review.
5:30 PM – The Secure Final Approval
Before heading out, Elara needs to approve a big code deployment.
How it Works: The deployment system (an agent) asks for Elara’s sign-off. The Fabric requires super-secure authentication. Forget a simple password. Elara’s corporate ring (a device) must be within range of her laptop (another device), and she has to confirm with a fingerprint or verifiable credential. This ties the approval to a specific location and two authenticated devices, a rock-solid application of the Zero Trust principle, all thanks to the Fabric.
7:00 PM – Time for Personal Life
Back home, Elara switches from her work profile to her personal one on the exact same foldable device.
How it Works: The Fabric instantly kills all corporate access tokens and shuts down the VDI session. Then, it creates a completely separate, firewalled personal environment. Her smart TV connects to her personal media server using tokens that are totally isolated from the corporate stuff. The Access Fabric makes sure Elara’s work and personal lives stay completely separate and secure, even when using shared hardware, wrapping up another day of dynamic, context-aware access.
Example of an Access Fabric using Microsoft: Future View
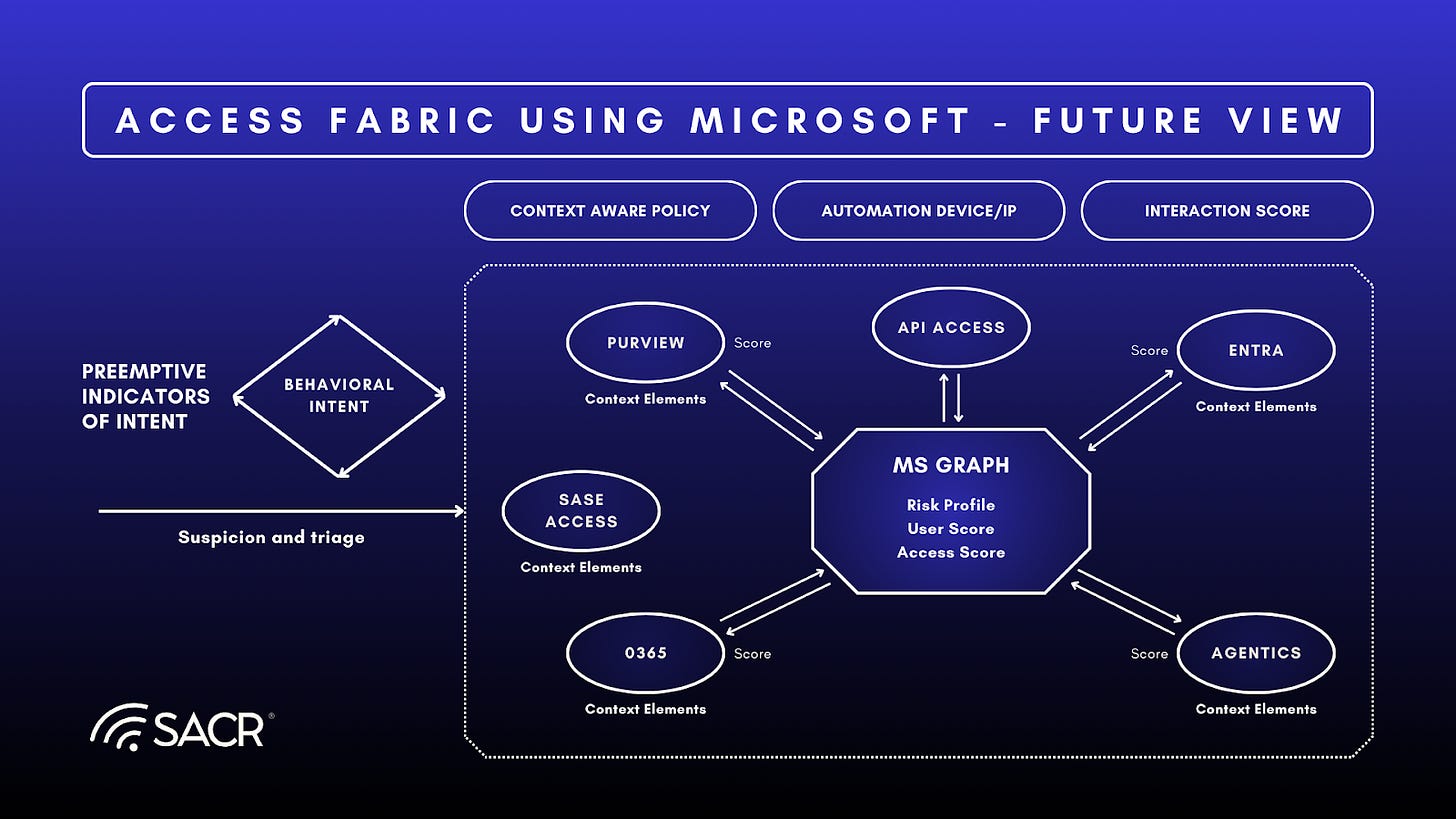
Current State Profile: Microsoft as an Access Fabric
Below is a practical current state profile mapped to our A/B/C/D layers. This is intentionally framed as elements (not a single product claim), because our note positions Access Fabric as an architecture. Microsoft, with its robust suite of security and identity products like Microsoft Entra, Defender, and Purview, largely aligns with the architectural outcomes of our vendor-agnostic Access Fabric due to its strong identity governance and comprehensive cloud ecosystem integration. However, achieving complete alignment presents challenges and evolutions stemming from its nature as a massive platform provider.
Microsoft’s focus is naturally securing its own ecosystem, potentially leading to some friction when integrating non-Microsoft, best-of-breed tools into the Fabric’s unified policy layer, which can create incomplete coverage for specialized, niche security outcomes or proprietary legacy systems. While Microsoft provides the necessary security elements (the inputs), the full realization of the Access Fabric’s seamless, integrated data and control plane often requires additional significant customer-side integration and orchestration, meaning Microsoft facilitates the architecture rather than providing the final, holistic Fabric itself, at least currently.
Below we articulate the current state and some guidance on moving to the Access Fabric vision within the Microsoft architecture.
Layer A — Identity & Context Plane (Subject)
Current state (typical Microsoft estate)
- Strong human identity core, agent and device context signals are generally available.
- Non-human identities exist in large numbers, but are usually managed inconsistently (service principals, workloads, automation accounts, agent identities).
Opportunities for Improvement
- A unified identity directory is more directory + scattered NHI stores than a single normalized identity fabric for humans + NHIs + agents. Agent identities also have a registry where non-auth related data and biz data will be.
- Workload attestation (SPIFFE-like posture) is not consistently a default across enterprise workloads in most environments.
Layer B — Intelligence & Policy Plane (Brain)
Current state
- Many customers have partial risk engines, but they are often scoped to:
- identity sign-in risk
- endpoint risk
- data risk
- rather than one unified, continuously re-evaluated decision brain, which tools like conditional access can help unify
Opportunities for Improvement
- Unified policy management is still fragmented across security domains and consoles (identity policies, endpoint policies, network policies, data policies). This is being addressed by expanding use cases of Microsoft Entra into one policy engine with signals across threat detection and data protection integrated.
- Intent is mostly implicit (detections after the fact) vs. explicit (modeled, tracked, and used preemptively).
Layer C — Orchestration & Interoperability (Weave)
Current state
- Microsoft-centric environments can integrate identity and SaaS apps well (OIDC/SAML/SCIM patterns), but hybrid and multi-vendor identity is still common.
- Orchestration exists, but often as point-to-point connectors and manual workflows.
Opportunities for Improvement
- The weave is not a real-time bidirectional loop where any signal can immediately trigger enforcement everywhere (our fabric thesis).
- Legacy translation is uneven. Many orgs still have exceptions that become the attacker’s path.
Layer D — Enforcement & Connectivity (Edge)
Current state
- Enforcement is strong in several places, but it is not uniformly universal ZTNA for everything.
- Many enterprises still have VPN, flat network segments, and uneven app-level enforcement.
Opportunities for Improvement
- Lateral movement is reduced in pockets, but not eliminated end-to-end.
- Enforcement actions are not always “computed centrally and pushed instantly” based on new context/intent.
What Microsoft specific capabilities must evolve to achieve the end state (our fabric thesis)?
Here are the evolution requirements for Microsoft, where some evolution is needed to reach concrete capabilities that align Microsoft’s capabilities with our Access Fabric concept.
- From correlated alerts → correlated decisions
- Move from tools share logs to tools share live decisions and policy state, with tight latency expectations. Microsoft Security tools (Entra Identity Protection, Defender, Purview) share data in real time that are used for enforcement/policy decisions.
- From identity risk → transaction trust
- Trust must be computed per-request, continuously, and revoked mid-session based on new signals (our continuous verification uplift). With Microsoft Agent identity risk is computed in across all signals in realtime and is in preview.
- From NHI sprawl → first-class agent/workload identity
- Normalize NHIs and AI agents into the same governance model as humans. See Entra Agent ID IGA – in preview.
- Add workload identity attestation patterns so “what is calling” is cryptographically provable, not asserted.
- From context signals → an Access Graph with defined outputs
- The Access Graph should emit:
- an access decision (allow/step-up/limit/block),
- a continuously updating access score,
- a policy adjustment recommendation,
- and (critically) an intent assessment for both humans and agents.
- The Access Graph should emit:
- From reactive detections → preemptive intent indicators
- Our PIIB vision of the future becomes the differentiator if anchored to:
- what signals count as preemptive (predictive intelligence, deception signals, reputation and IoC feed lead data, or intent signal from LLM interactions)
- how they are validated to avoid hallucination risk
- what enforcement patterns they trigger (step-up auth, token scoping, data sandboxing, session quarantine).
- Our PIIB vision of the future becomes the differentiator if anchored to:
- From policy fragmentation → a unified policy control plane
- Even if the estate is multi-vendor, the end state needs a single place where the truth of access policy is expressed and then enforced consistently everywhere. Microsoft Conditional Access in Entra enhances and provides this functionality.
Market Implications of an Access Fabric
Future View of Microsoft Access Fabric Evolution
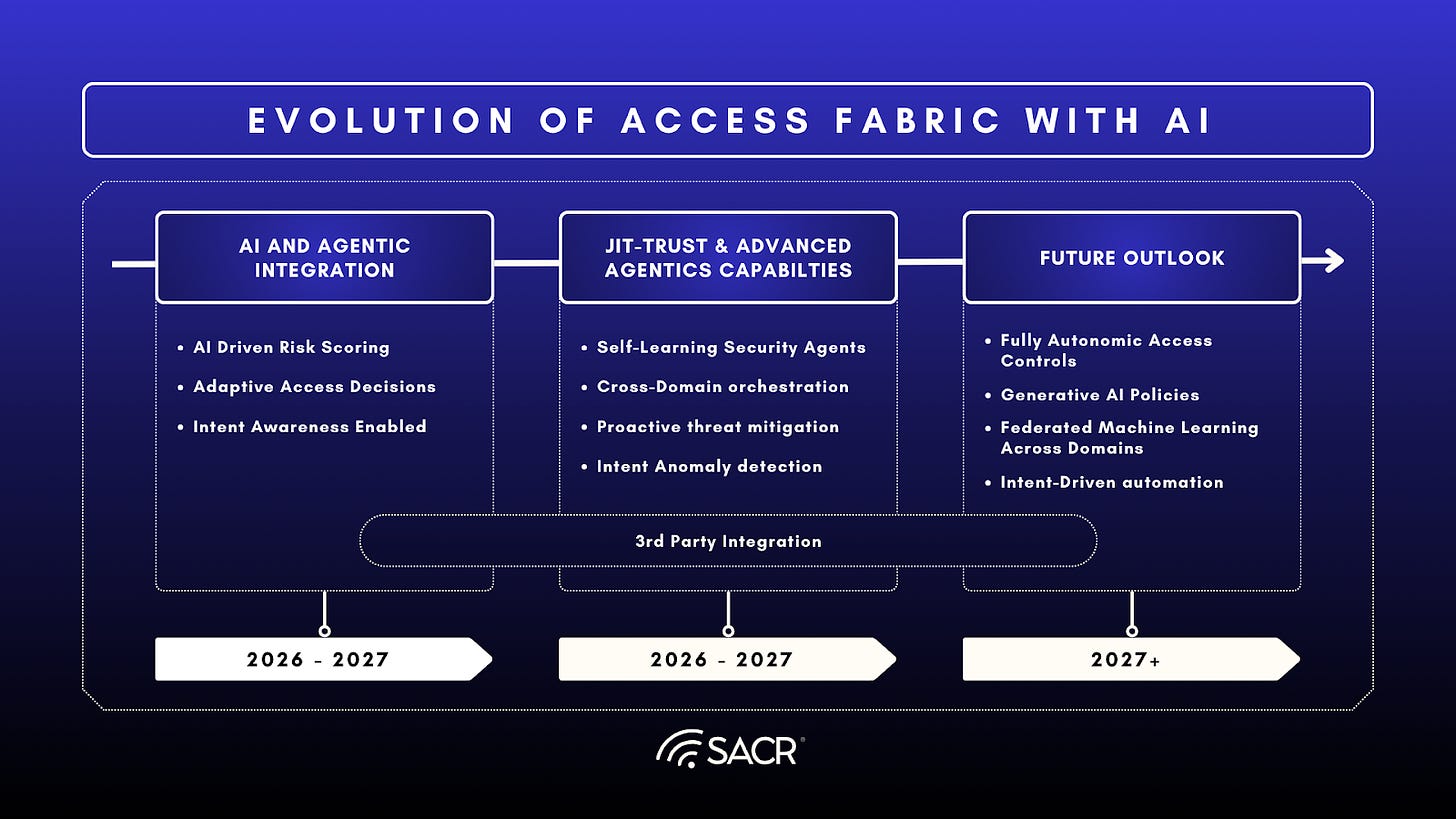
Self-Learning Security Agents with Intent Modeling Emerges
Based on utilizing JIT-TRUST (See JIT-TRUST) we expect agentics to drive intent modeling by evolving beyond simple historical data, these self-learning agents leverage intent modeling and federated learning to understand the why behind user actions without compromising raw data privacy. This approach allows the system to construct dynamic intent profiles, digital twins that adapt as a user’s role changes,moving security from a reactive stance to a proactive one. Rather than just flagging a breach after it occurs, these agents can detect subtle behavioral shifts, such as an employee accessing sensitive files for the first time, or predict high-risk actions like unauthorized data exports before they are initiated.
Intent Aware Access Fabrics offer significant market advantages including:
- True Zero Trust Realization
- Autonomous Access Governance
- Reduced Operational Complexity
- Generative AI for Policy Creation & Justification
- Seamless Cross-Domain Orchestration
- Privacy-First Intent Inference
- Human-in-the-Loop as a Strategic Asset
True Zero Trust Realization
The Fabric moves Zero Trust from a static configuration only considering basic threat, risk and posture to a dynamic, continuous preemptive (predictive) runtime behavioral operation that can consistently deliver adjustments based on intent to trust and permissions of access, control and execution of agentic and user operations across the environment.
Autonomous Access Governance
Access decisions will be made not by IT teams or security analysts, but by a distributed network of autonomous AI agents, each operating as a specialized trust node within the fabric. Representing a key integration capability for third party Agentic Access Governance agents, both delivered by third parties or by Microsoft.
- These Autonomous Access Governance agents will likely:
- Monitor user behavior in real time
- Infer intent from context (location, device, app usage, network path)
- Automatically grant, revoke, or modify access based on dynamic policies
- Escalate only when uncertainty exceeds predefined thresholds
Reduced Operational Complexity
By centralizing policy intelligence within Microsoft Graph or other Graph concepts, organizations gain a significant advantage in managing and enforcing security and compliance. This consolidation dramatically reduces the complexity and overhead associated with maintaining multiple, potentially conflicting, or redundant policy sets scattered across various disconnected security and IT management tools.
- Instead of requiring administrators to manually synchronize updates and changes across disparate systems, which is often a process prone to human error and inconsistency, the unified approach ensures a single source of truth for access, governance, and compliance policies.
- This centralization fosters a more coherent and robust security posture, enabling more consistent application of rules for data access, resource utilization, an user behavior, which is particularly crucial in the modern, hybrid, and multi-cloud environment where users and data are highly distributed.
Generative AI for Policy Creation & Justification
Organizations are shifting toward natural language policy definition, leveraging generative AI to translate simple prompts into complex, precise conditional access rules. Microsoft Entra has a Conditional Access Policy Optimization Agent which is continuously evaluating tenant security posture and making recommendations to policy to improve it. This shift democratizes security by allowing non-technical departments, such as HR or Finance, to manage access requirements through intuitive commands while the system handles the heavy lifting of backend configuration and automated justification.
- Provides clear rationales for every access decision.
- Maintains full audit trails for human review.
- Ensures security remains rigorous yet accessible.
- Effectively removes the technical bottleneck traditionally associated with IT policy management.
- Provides suggested rollout of new policy or change in policy across the organizations user base
Seamless Cross-Domain Orchestration
Acting as the central nervous system of enterprise security, the Access Fabric creates a unified trust layer by integrating identity, network, cloud workloads, and endpoints into a single, cohesive ecosystem.
- This framework moves beyond siloed security by using real-time orchestration to evaluate risk and intent across hybrid and multi-cloud environments, for instance, automatically determining if a remote login matches a known travel event.
- By dynamically adjusting permissions, such as granting temporary, read-only access for verified risks or triggering immediate blocks for anomalies, the system ensures that security policies are enforced consistently from the local edge to the deep cloud.
Privacy-First Intent Inference
To ensure rigorous compliance with global regulations like GDPR and HIPAA, intent modeling is anchored in privacy-preserving architectures that prioritize data sovereignty. By utilizing federated learning and differential privacy, the system can train sophisticated behavioral models without ever centralizing sensitive raw data, often performing inference directly on the user’s device.
- This transparent approach provides users with clear insights into how their actions align with their unique intent profiles, fostering a culture of trust rather than surveillance.
- By demystifying security decisions through plain-language justifications, organizations can significantly reduce user friction and accelerate the adoption of advanced protective measures.
Human-in-the-Loop as a Strategic Asset
Rather than replacing human judgment, AI agents serve to elevate it by filtering through the noise to highlight high-risk or ambiguous intent events that require nuanced intervention. By providing rich context, such as correlating an unsecured Wi-Fi connection with specific data access patterns, the system empowers analysts with actionable intelligence and suggests next steps.
- Move away from the fatigue of reactive monitoring
- Focus expertise on investigating complex anomalies
- Mitigate insider threats
- Manage long-term policy drift
Vendor Consolidation vs. Ecosystem Integration
The market will favor vendors who can either provide the entire Fabric or vendors whose products can seamlessly plug into a dominant Access Graph via robust APIs, a converged identity control plane and intent and behavioral awareness at scale, in a real-time manner.
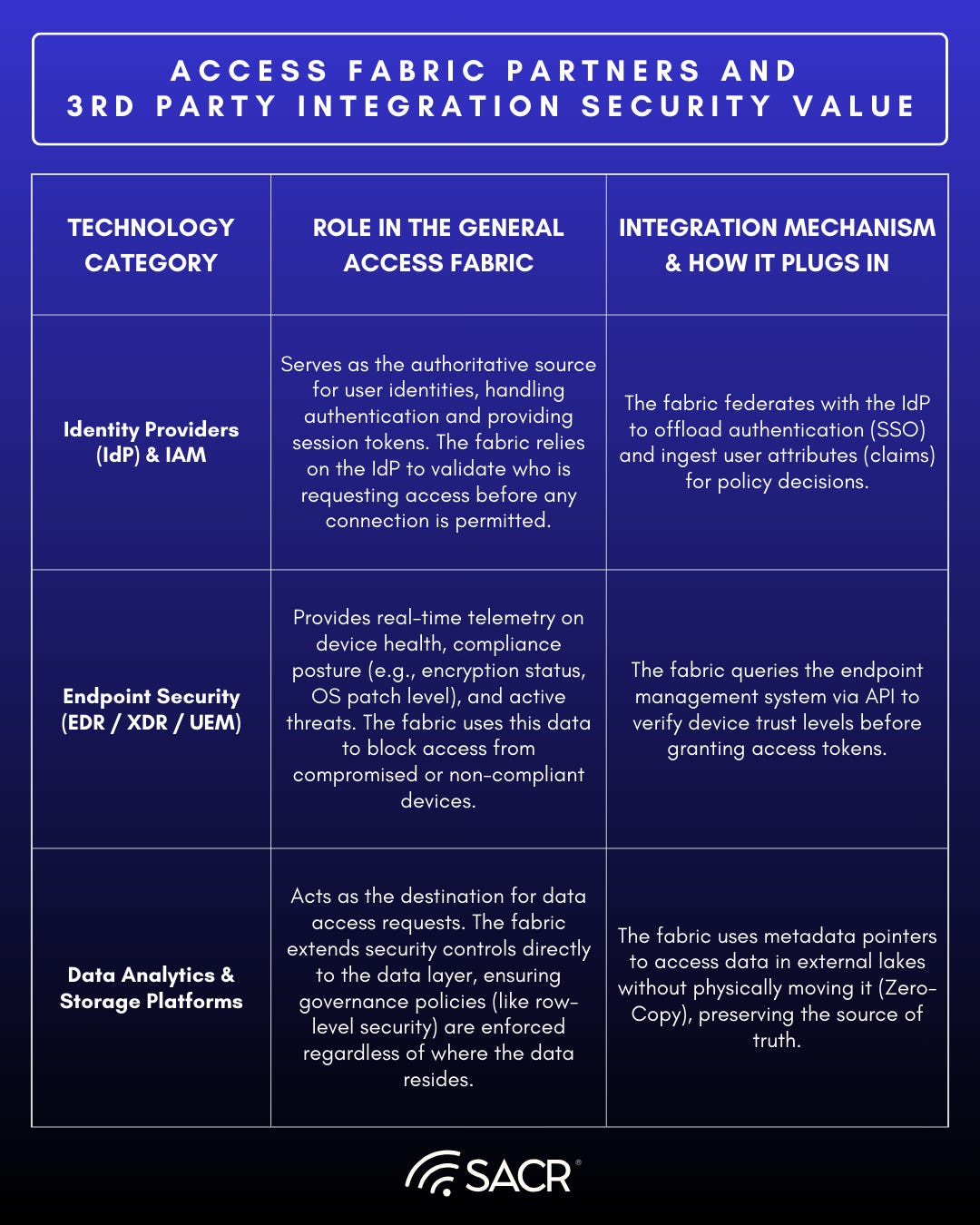
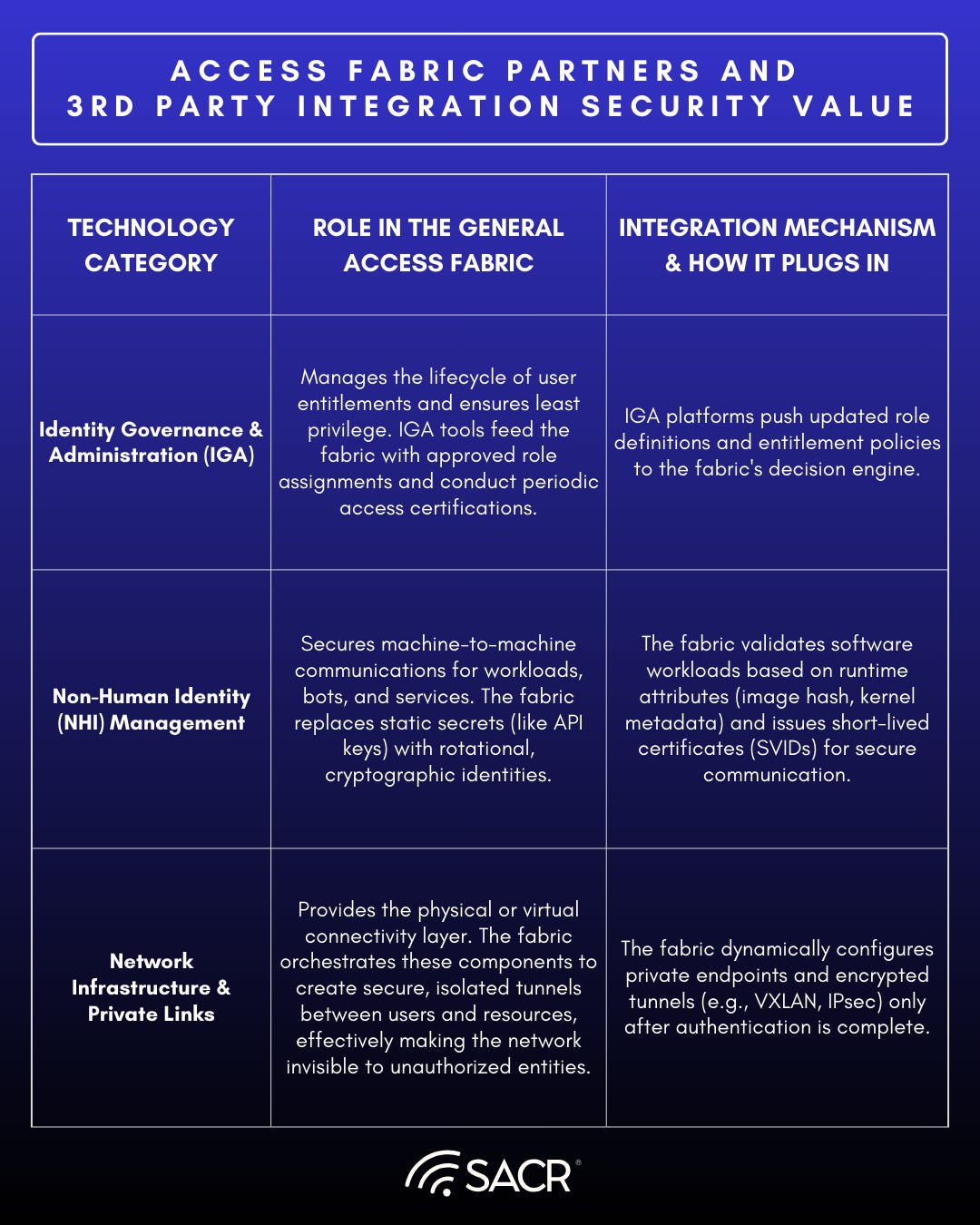
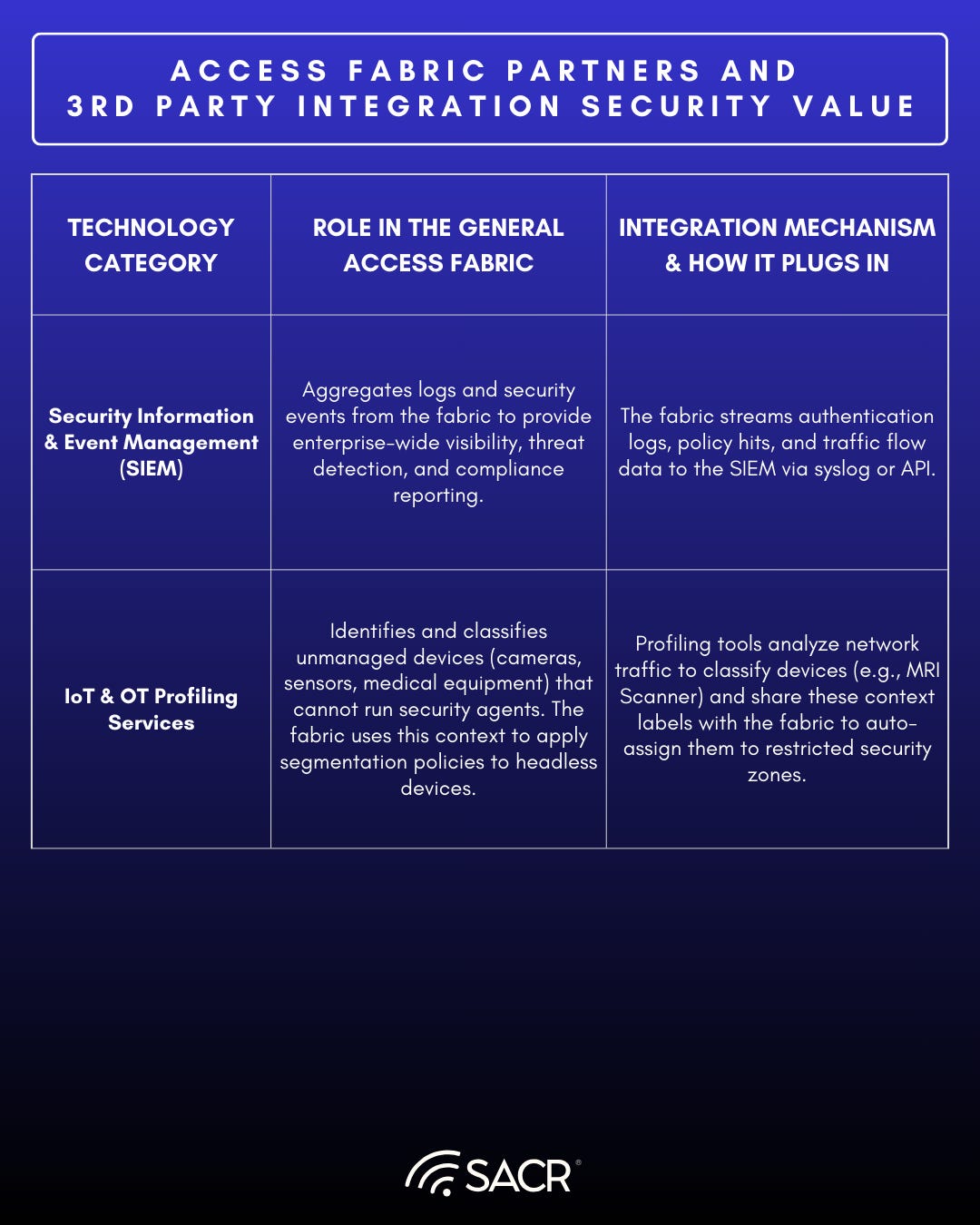
Access Fabric Partners and Third Party Integration Security Value
SACR Key Takeaways:
Access Fabrics represent a necessary maturation of Zero Trust architectures. By utilizing an Access Graph and intent extraction with large language models, we can unify signals from Identity, Network, and Data, Endpoint Behaviors, and SOC events so that organizations can create a more resilient, adaptive real-time security posture. The future belongs to platforms that can successfully weave these disparate threads into a single, intelligent fabric that understands not just who is asking for access, but the entire context and intent surrounding the request. This representation moves cybersecurity from a static set of gates to an adaptive, intelligent organism that evolves with the threat landscape.